Threat landscape for smart buildings
The Kaspersky Industrial Cybersecurity Conference 2019 takes place this week in Sochi, the seventh such conference dedicated to the problems of industrial cybersecurity. Among...
How to Operationalize the Zero Trust Security Pillar ‘Limit Access & Privilege’ with ServiceNow
An easy way for a cyber-attacker to gain access to sensitive data is by compromising an end user’s identity and credentials. Things get even...
Spam and phishing in Q2 2018
Quarterly highlights
GDPR as a phishing opportunity
In the first quarter, we discussed spam designed to exploit GDPR (General Data Protection Regulation), which came into effect...
Gartner Names PAM a Top Security Project (AGAIN!) in 2019
Last June at the 2018 Gartner Security & Risk Management Summit, the analyst firm issued a “Smarter with Gartner” paper outlining the Top 10...
Incident Response report 2018
Download full report (PDF)
Introduction
This report covers our team’s incident response practices for the year 2018. We have thoroughly analyzed all the service requests, customer...
Stop Breaches with Analytics and Artificial Intelligence
According to Gartner, companies will spend up to $96 billion worldwide on security this year, but research by Centrify and Dow Jones suggests that...
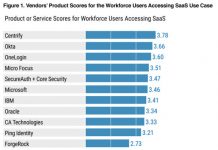
Centrify Scores Highest for Both “Workforce Users Accessing SaaS” and “Business-to-Business” in New Gartner...
Gartner just released their first ever “Critical Capabilities for Access Management, Worldwide, 2018” report, and we are proud to see that Centrify has scored...
Large-scale SIM swap fraud
Introduction
SIM swap fraud is a type of account takeover fraud that generally targets a weakness in two-factor authentication and two-step verification, where the second...
Identity-Based Security Comes of Age at Infosec18
The annual Infosecurity Europe (Infosec) show was back again at the start of June even bigger and better than before. This year it was...
World Password Day – 5 Facts About Weak Credentials
Happy World Password Day!
Ok, I’ll admit until a few days ago, I wasn’t aware this was a thing. As with most events in my...