ATM robber WinPot: a slot machine instead of cutlets
Automation of all kinds is there to help people with their routine work, make it faster and simpler. Although ATM fraud is a very...
Time of death? A therapeutic postmortem of connected medicine
#TheSAS2017 presentation: Smart Medicine Breaches Its “First Do No Harm” Principle
At last year’s Security Analyst Summit 2017 we predicted that medical networks would be...
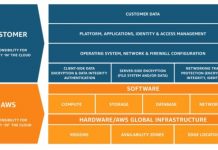
Zero Trust Security and DevOps Take the Crown at AWS Public Sector Summit 2018
Last week, Amazon Web Services hosted its AWS Public Sector Summit in Washington, DC. In its 9th year, the event attracted thousands of global...
Adopt Next-Gen Access to Power Your Zero Trust Strategy
Security breaches are now all too commonplace — 58% of organizations have experienced at least one in the past 12 months. As a result,...
Spam and phishing in 2017
Figures of the year
The share of spam in mail traffic came to 56.63%, down 1.68% against 2016.
The biggest source of spam remains the US...
3 for 3! Centrify a Leader in 2019 KuppingerCole Leadership Compass for PAM
KuppingerCole recently published its 2019 KuppingerCole Leadership Compass for Privileged Access Management (PAM), again recognizing Centrify as a Leader as it did in the...
Centrify Zero Trust Security Partners in the Spotlight at RSA Booth 501
RSA Conference has moved back to April this year, and next week the largest cybersecurity trade show in the world will once again convene...
Five Best Practices for Zero Trust Security
The Centrify Zero Trust Security model is effective because it allows organizations to remove trust from the equation entirely. Based on the assumption that...
Zero-day in Windows Kernel Transaction Manager (CVE-2018-8611)
Executive summary
In October 2018, our AEP (Automatic Exploit Prevention) systems detected an attempt to exploit a vulnerability in the Microsoft Windows operating system. Further...