A Leader in the 2019 Gartner Magic Quadrant for WAF, Six Years Running
Gartner has published its 2019 Gartner Magic Quadrant for Web Application Firewalls (WAF) and Imperva has been named a Leader for the sixth consecutive...
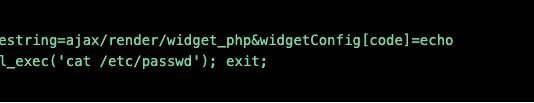
A Deep Dive into Database Attacks [Part I]: SQL Obfuscation
Today, data breaches are a threat to every organization. According to a report from Risk Based Security covering the first half of 2017, over 6...
Configuring Imperva SecureSphere for GDPR Compliance: Part One
Time is running out. 23 days until GDPR enforcement
The GDPR effective date is less than a month away and, given the significant risk and...
Imperva Recognized as a 2018 Gartner Magic Quadrant WAF Leader, Five Years Running
Gartner has named Imperva as a Leader in the 2018 Gartner Magic Quadrant for Web Application Firewalls (WAF) — for the fifth year in...
72 Hours: Understanding the GDPR Data Breach Reporting Timeline
We’re down to the wire with respect to the General Data Protection Regulation (GDPR) compliance deadline of May 25, 2018.
Organizations that fail to comply...
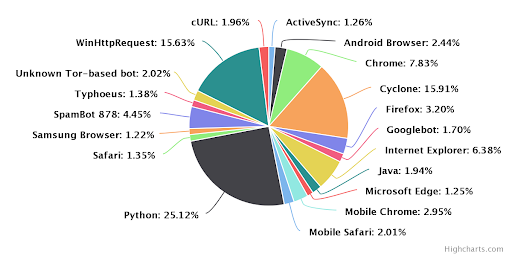
SQL Injection Attacks: So Old, but Still So Relevant. Here’s Why (Charts)
We’re living in the Golden Age of data. Some companies analyze it to better themselves, others trade it for profit, none give it up...
E-commerce: Bad bots are ready for the holidays. Are you?
The busiest time for online retailers is almost upon us—the holiday season. Each business is looking at ways to take advantage of cyber week...
Making the Grade: Achieve SSL Labs A+ Grade with Imperva WAF
We all woke up to a new reality early last year. HTTPS adoption has reached the tipping point, meaning that more than half of...
Data Security Solutions for GDPR Compliance
Enforcement of the new EU General Data Protection Regulation (GDPR) adopted in 2016 starts on May 25, 2018. It requires all organizations that do...
APIs Ease Customer Interaction — and External Attacks. Here’s how to Protect Them.
To deliver seamless service experiences to our customers, businesses now rely heavily on application programming interfaces (APIs). These are a non-negotiable aspect of the...


![A Deep Dive into Database Attacks [Part I]: SQL Obfuscation](https://www.dataproof.co.za/wp-content/uploads/2018/02/a-deep-dive-into-database-attacks-part-i-sql-obfuscation-218x150.png)