CVE-2026-42945: Imperva Customers Protected Against Critical NGINX Rewrite Module Vulnerability
TL;DR: Researchers recently disclosed CVE-2026-42945, a critical heap-based buffer overflow vulnerability affecting both NGINX Open Source and NGINX Plus. The flaw exists within the...
Why AI Agents Make API Security a CISO Priority
AI agents are not a future concern. They are already changing how enterprise systems are accessed, automated, and abused.
And the security implication is clear:...
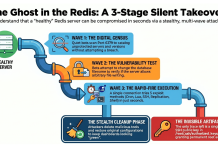
Your Redis Server Looks Fine. That’s the Problem.
Introduction
There’s an automated attack circulating right now that breaks into unprotected Redis servers, takes over the underlying machine, and then carefully puts everything back...
Imperva Customers Protected Against CVE-2026-41940 in cPanel & WHM
What is CVE-2026-41940?
CVE-2026-41940 is a critical authentication bypass vulnerability affecting cPanel & WHM, including DNSOnly, in versions after 11.40. The flaw, discovered by WatchTowr...
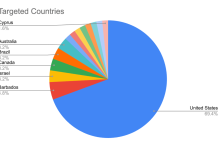
Bad Bot Report 2026: The Internet Is No Longer Human and It’s Changing How...
For decades, companies have operated on a simple assumption that most internet traffic came from people. That assumption no longer holds.
The latest 2026 Bad...
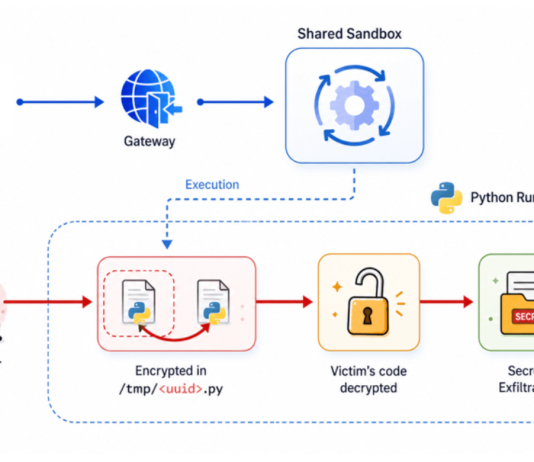
Hacking Safari with GPT 5.4
When Anthropic unveiled Mythos and Project Glasswing, the reaction was immediate and polarized. Some dismissed it as fear-driven marketing, while others treated it as...
Anthropic Mythos: Separating Signal from Hype
The recent buzz around Anthropic’s Mythos model has been intense, and for good reason. Early reports suggest a model that significantly advances automated reasoning over large codebases,...
React2DoS (CVE-2026-23869): When the Flight Protocol Crashes at Takeoff
Executive Summary
In this article, we disclose a new high severity unauthenticated remote denial‑of‑service vulnerability we identified and reported in React Server Components that we’ve...
API Security for AI Agents: Why Protection Has Never Been More Important.
For years, a lot of risky APIs survived simply because they were hard to find. They weren’t documented. Only a handful of engineers knew...
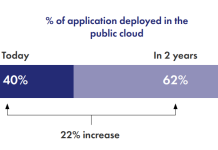
Securing Applications Anywhere: Breaking Down the Wall of Confusion
Application development has changed dramatically. Enterprises now release software faster, operate more digital services, and deploy applications across a mix of public cloud, private...