Metasploit Wrap Up 05/29/2026
More Linux LPEsHark the age of the Linux LPE has arrived. This week’s release follows up on recent work bringing new Linux LPEs to...
Rapid7 Observed Exploitation of PAN-OS GlobalProtect Authentication Bypass Vulnerability (CVE-2026-0257)
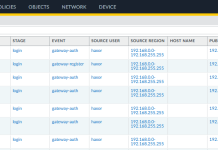
OverviewOn May 13, 2026, Palo Alto Networks published a security advisory for CVE-2026-0257, a medium severity authentication bypass affecting PAN-OS and Prisma Access when...
How Security Leaders Cut Through Complexity to Drive Better Outcomes
Security leaders are operating in an environment that is only getting more complex. Expanding attack surfaces, rapid AI adoption, growing toolsets, and increasing pressure...
Metasploit Wrap Up 05/22/2026
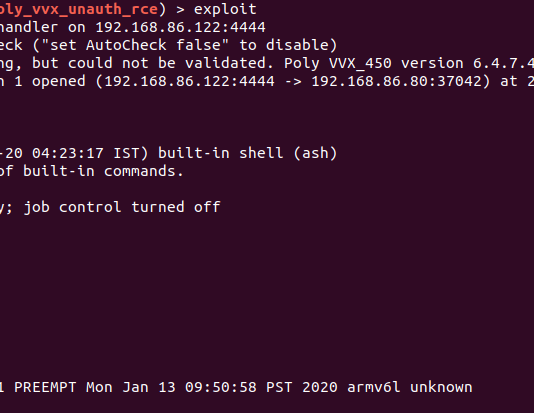
Another week, another authentication bypassOur humble Metasploit weekly(ish) blog has been blessed with a new network component vulnerability. The dynamic duo of @sfewer-r7 and...
Q1 2026 Threat Landscape Report: Zero-clicks, geopolitical tensions, and some wins for law enforcement
The first quarter of 2026 reinforced that attackers are moving faster, operating with greater coordination, and exploiting weaknesses before most organizations can respond effectively....
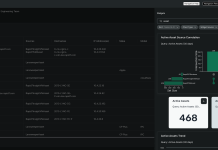
Operationalizing CTEM Faster: Build Surface Command Dashboards in Minutes
Modern attack surfaces don’t sit still.Cloud expansion, SaaS sprawl, identity complexity, and shadow IT are continuously reshaping organizational risk. For security leaders, visibility isn’t...
Rapid7’s 2026 Global Cybersecurity Summit: Key Takeaways for Security Leaders
Security teams are working in an environment where speed, scale, and complexity are all increasing at the same time. Across the Rapid7 2026 Global...
Metasploit Wrap-Up 05/15/2026
Weaponizing a text editor for fun and profitGather round, dear readers, because today, we (by we, we mean @h00die) dropped the ultimate persistence mechanism:...
CVE-2026-0265: Authentication Bypass in Palo Alto Networks PAN-OS
OverviewOn May 13, 2026, Palo Alto Networks published a security advisory for CVE-2026-0265, a signature verification vulnerability that facilitates authentication bypass on PAN-OS, the...
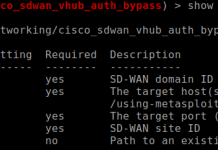
CVE-2026-20182: Critical authentication bypass in Cisco Catalyst SD-WAN Controller (FIXED)
OverviewWhile researching a critical authentication bypass vulnerability, CVE-2026-20127, which was exploited in-the-wild, Rapid7 Labs discovered a new authentication bypass vulnerability affecting Cisco Catalyst SD-WAN...