What do Equifax, HBO, Uber and Yahoo All Have in Common?
A consumer ratings agency, a cable network, a transportation company and a web services provider. What ties them together? Sure, they were all impacted...
Every little bitcoin helps
It often happens that inventions and technologies that start out good end up turning into dangerous tools in the hands of criminals. Blockchain is...
Cybercriminals target early IRS 2018 refunds now
On Monday, Jan 29th, IRS officially opened its 2018 season. Some taxpayers already filed their taxes and cybercriminals know it too. So, right after...
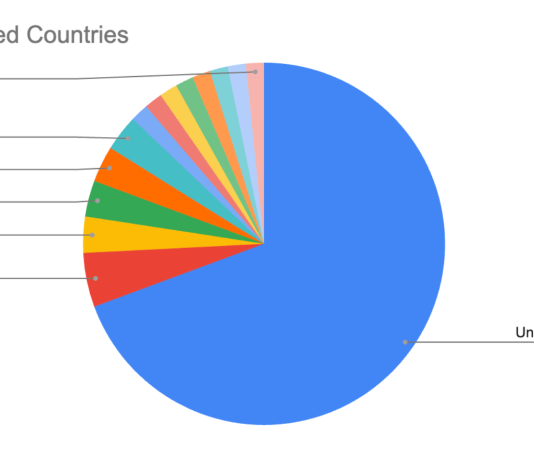
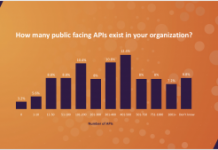
Survey: APIs a Growing Cybersecurity Risk
Like a lot of people, your mobile phone number is probably easily accessible to anyone with a bit of searching. Imagine if someone could...
Improve the ROI of Your Database Protection Investment
When an organization considers switching a mission-critical compliance or security system from one vendor’s solution to another it’s a very big decision. There is...
Denis and Co.
In April 2017, we published a detailed review of a malicious program that used DNS tunneling to communicate to its C&C. That study prompted...
Centrify to Discuss Zero Trust Security at the ICIT 2018 Winter Summit
Following the high-profile breach of the US Office of Personnel Management (OPM), which exposed the personal data of millions of Americans, the House of Representatives’...
4 Months to Go: A New Year GDPR Checklist
As we enter the New Year, IT and security leaders have most likely been glued to revelations of major new CPU-level vulnerabilities Meltdown and...
Data Breaches Plague Organizations for Years
Once an organization’s network is breached, extinguishing the flames is just the first step in a long, painful and costly journey to recovery. There’s...
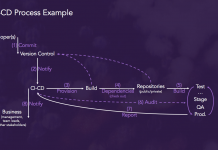
Security Strategies for DevOps, APIs, Containers and Microservices
More and more IT professionals see DevSecOps, a practice which integrates security measures earlier in the development process to improve production code quality, as...