Integrate Your Ticketing System into Database Security to Prevent DBA Privilege Abuse
Many of the recent high-profile data security breaches were made by trusted insiders. They are often database administrators (DBAs) who are highly privileged and...
Five Best Practices for Zero Trust Security
The Centrify Zero Trust Security model is effective because it allows organizations to remove trust from the equation entirely. Based on the assumption that...
A Deep Dive into Database Attacks [Part I]: SQL Obfuscation
Today, data breaches are a threat to every organization. According to a report from Risk Based Security covering the first half of 2017, over 6...
RSA 2018
RSA 2018
Digital Guardian will be exhibiting at RSA 2018. Discover all the things happening at our booth and beyond!
...
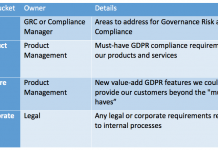
One GRC Manager’s Practical Approach to GDPR Readiness
With about four months to go before the GDPR becomes effective many companies are still struggling with where to start. You’re not alone. According...
A vulnerable driver: lesson almost learned
Recently, we started receiving suspicious events from our internal sandbox Exploit Checker plugin. Our heuristics for supervisor mode code execution in the user address...
Zero Trust Security for the New Australian Data Breach Law
Many Australian businesses need to rethink their approach to security to prepare for their nation’s new mandatory data breach notification law which take effect...
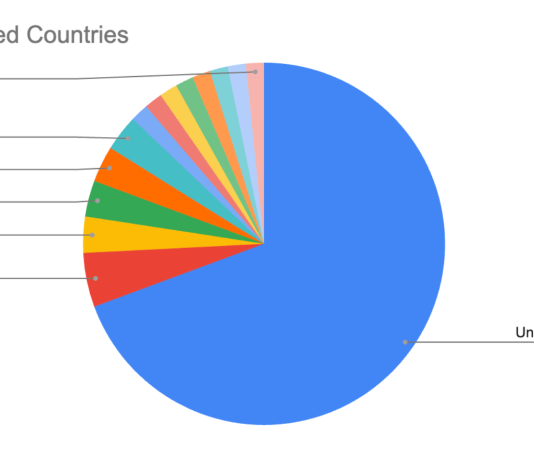
Gas is too expensive? Let’s make it cheap!
A few months ago, while undertaking unrelated research into online connected devices, we uncovered something surprising and realized almost immediately that we could be...
Escaping Data-Breach Groundhog Day
Countless companies globally are trapped in data breach Groundhog Day, unable to escape a repeating cycle of cyber attacks.
In the 2018 Thales Data Threat...
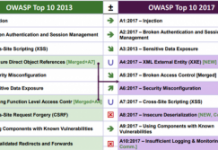
2017 OWASP Top 10: The Good, the Bad and the Ugly
Since its founding in 2001, the Open Web Application Security Project (OWASP) has become a leading resource for online security best practices. In particular,...




![A Deep Dive into Database Attacks [Part I]: SQL Obfuscation](https://www.dataproof.co.za/wp-content/uploads/2018/02/a-deep-dive-into-database-attacks-part-i-sql-obfuscation-218x150.png)