The Emerging Importance of Securing Access to AWS
With 50,000 attendees, over 1,000 breakout sessions and countless sponsors and exhibitors, the 2017 AWS re:Invent conference in Las Vegas was one of the...
Skygofree: Following in the footsteps of HackingTeam
At the beginning of October 2017, we discovered new Android spyware with several features previously unseen in the wild. In the course of further...
State of App Delivery 2018: Security Again Edges Out Availability As Most Important App...
Forty-three percent of organizations say security is essential when deploying apps, and more than two thirds use multiple security solutions to protect clients, infrastructure,...
Data Privacy Day
- Read more
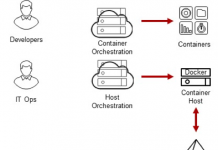
Centrify Identity Services: Securing Docker and Containers
Introduction
We are excited to announce that Centrify now supports CoreOS Container Optimized Linux which several of our customers are using as part of their...
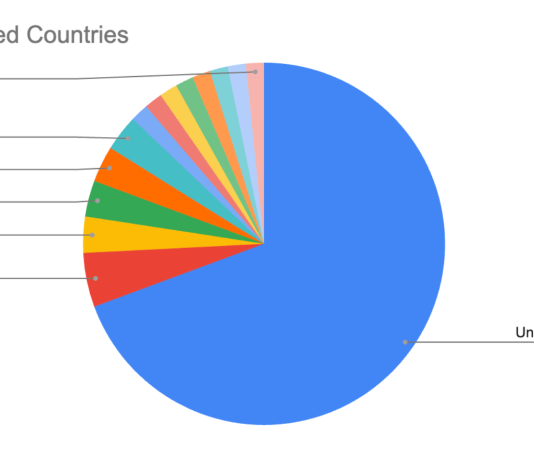
Cloud Database Migration Peer Insights [Report]
Not long ago, for security, compliance or other reasons, it was unthinkable for many regulated organizations to move sensitive data into the cloud. It’s...
4 Steps to Reduce the Risk of Shared Account Passwords
Reduce the Risk of a Security Breach When Sharing Privileged Accounts
There are partners, employees, contractors, customers and others who access or try to access...
KLAS Findings on Healthcare DLP Strategies
KLAS Findings on Healthcare DLP Strategies
This webinar was recorded on December 19, 2017.
- Read more
Cloud Migration Fundamentals
The advantages offered by a cloud-based environment make it an easy decision for most companies to make. Still, there are numerous critical choices to...
Centrify Predicts: Cybersecurity in 2018
As we start 2018, we have continued to see major breaches across industries, only last year we witnessed at least two companies — Uber...






![Cloud Database Migration Peer Insights [Report]](https://www.dataproof.co.za/wp-content/uploads/2018/01/cloud-database-migration-peer-insights-report-218x150.png)












