[R2] Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2:...
Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2: SC-202602.1 + SC-202602.2 Arnie Cabral Tue, 02/17/2026 - 08:32
Security...
Siemens Simcenter Femap and Nastran
View CSAF
Summary
Siemens Simcenter Femap and Nastran is affected by multiple file parsing vulnerabilities that could be triggered when the application reads files in NDB...
Western cyber alliances risk fragmenting in new world order
The conduct of powerful nations is causing knock-on effects in the cyber world as long-standing security frameworks appear increasingly precarious - Read more
Divide and conquer: how the new Keenadu backdoor exposed links between major Android botnets
In April 2025, we reported on a then-new iteration of the Triada backdoor that had compromised the firmware of counterfeit Android devices sold across...
Invitation to Trouble: The Rise of Calendar Phishing Attacks
By: Adrian Andaya and Gabriel Mamaril, Cofense Phishing Defense CenterBefore you click “Accept” on calendar invites, think twice — it could be a phishing...
Canada Goose – 581,877 breached accounts
In February 2026, a data breach allegedly containing data relating to Canada Goose customers was published publicly. The data contained 920k records with 582k...
Unlocking business resilience with full-stack observability in hybrid IT environments
Full-stack observability helps Gulf IT leaders accelerate ROI, strengthen resilience, and advance digital maturity. Learn how to use AI-driven insights and automation to align...
University of Pennsylvania – 623,750 breached accounts
In October 2025, the University of Pennsylvania was the victim of a data breach followed by a ransom demand, largely affecting its donor database....
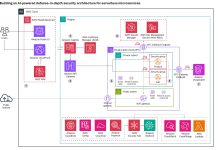
Building an AI-powered defense-in-depth security architecture for serverless microservices
Enterprise customers face an unprecedented security landscape where sophisticated cyber threats use artificial intelligence to identify vulnerabilities, automate attacks, and evade detection...
Fake CAPTCHA Scam Tricks Windows Users Into Installing Malware
A fake CAPTCHA scam is tricking Windows users into running PowerShell commands that install StealC malware and steal passwords, crypto wallets, and more.
The post...