[R1] Security Center Version 6.8.0 Fixes Multiple Vulnerabilities
Security Center Version 6.8.0 Fixes Multiple Vulnerabilities Arnie Cabral Wed, 02/18/2026 - 08:32
Security Center leverages third-party software to help provide underlying functionality....
“Good enough” emulation: Fuzzing a single thread to uncover vulnerabilities
A Cisco Talos researcher worked around the limitations of hardware-level Code Read-out Protection (RDP) on the Socomec DIRIS M-70 gateway by pivoting from physical debugging to...
Figure – 967,178 breached accounts
In February 2026, data obtained from the fintech lending platform Figure was publicly posted online. The exposed data, dating back to January 2026, contained...
DNS-PERSIST-01: A New Model for DNS-based Challenge Validation
When you request a certificate from Let’s Encrypt, our servers validate that you control the hostnames in that certificate using ACME challenges. For subscribers...
GrayCharlie Hijacks Law Firm Sites in Suspected Supply-Chain Attack
Executive Summary Insikt Group has been monitoring GrayCharlie, a threat actor overlapping with SmartApeSG and active since mid-2023, for some time, and is...
Cyber attacks enabled by basic failings, Palo Alto analysis finds
Cyberattacks are moving faster, shrinking the gap between initial compromise and bad consequences, and the advent of AI is accelerating...
Malware in the Wild as Malicious Fork of Legitimate Triton App Surfaces on GitHub
A malicious fork of the legitimate macOS application Triton has surfaced on GitHub, exploiting open-source repositories to distribute malware. The fraudulent repository, created...
AI in the Middle: Turning Web-Based AI Services into C2 Proxies & The Future...
Key Points
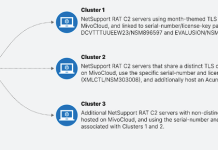
Check Point Research (CPR) has discovered that certain AI assistants that support web browsing or URL fetching can be abused as covert...