Ransomware Uses SYSTEM Scheduled Task to Encrypt Local Drives With Elevated Privileges
A newly analyzed ransomware strain called The Gentlemen is raising serious alarms across the cybersecurity community. Built in the Go programming language and...
CVE-2026-26168 Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
Updated an acknowledgement. This is an informational change only. - Read more
Silent Ransom Group Uses In-Person IT Impersonation to Breach Systems
Threat actors from the Silent Ransom Group, aka Luna Moth, are escalating attacks by impersonating IT staff in phone calls and even showing up...
Microsoft hits out over irresponsible vulnerability disclosure
Microsoft goes on the offensive after a disgruntled security researcher unleashed a series of zero-days without checking in first. - Read more
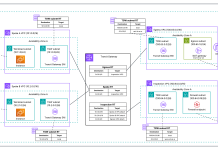
Why and how to migrate to a Transit Gateway-attached AWS Network Firewall
AWS Network Firewall now supports native attachment to AWS Transit Gateway. Customers commonly use Transit Gateway to route traffic from Amazon Virtual Private Cloud...
Charter – 4,851,517 breached accounts
In May 2026, the telecommunications company Charter Communications (the parent company behind the consumer broadband and cable brand Spectrum) was named by the ShinyHunters...
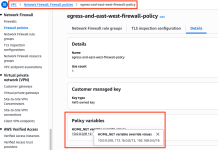
Simplifying policy management with URL and Domain Category filtering on AWS Network Firewall
Network administrators face a persistent challenge: maintaining domain blocklists and allowlists that keep pace with the internet. New websites and services emerge daily, and...
Less panic patching, more precision
Welcome to this week's edition of the Threat Source newsletter. Recently, Martin closed his introduction with a warning: Ready or not, the time of much patching...
ScadaBR – Multiple Vulnerabilities
ScadaBR - Multiple Vulnerabilities Multiple vulnerabilities affect ScadaBR. Tenable was unsuccessful in contacting the project. Recent publications indicate similar difficulty. CVE-2026-9645 Authenticated Remote Code Execution...
ABB EIBPORT
View CSAF
Summary
ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. A firmware update is available that resolves these...