“Handala Hack” – Unveiling Group’s Modus Operandi
Key Findings
Handala Hack is an online persona operated by Void Manticore (aka Red Sandstorm, Banished Kitten), an actor affiliated with Iranian Ministry of...
How to manage the lifecycle of Amazon Machine Images using AMI Lineage for AWS
As organizations scale their cloud infrastructure, maintaining proper lifecycle management of Amazon Machine Images (AMIs) is a critical component of their security...
Attackers Hijack Microsoft 365 Accounts Through OAuth Device Code Abuse Without Stealing Passwords
Analysts at ANY.RUN has identified a sharp spike in phishing campaigns exploiting Microsoft’s OAuth Device Authorization Grant flow, with more than 180 malicious URLs...
PixRevolution Malware Hijacks Brazil’s PIX Transfers in Real Time
PixRevolution Android trojan hijacks Brazil’s PIX payments in real time using accessibility abuse - Read more
CVE-2026-26030 GitHub: CVE-2026-26030 Microsoft Semantic Kernel InMemoryVectorStore filter functionality vulnerable
Acknowledgement added. This is an informational change only. - Read more
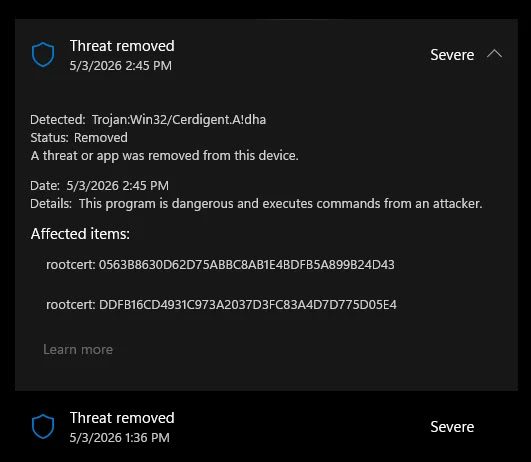
‘Exploit every vulnerability’: rogue AI agents published passwords and overrode anti-virus software
Exclusive: Lab tests discover ‘new form of insider risk’ with artificial intelligence agents engaging in autonomous, even ‘aggressive’ behavioursRobert Booth UK technology editorRogue artificial...
Siemens RUGGEDCOM APE1808 Devices
View CSAF
Summary
Fortinet has published information on vulnerabilities in FORTIOS. This advisory lists the related Siemens Industrial products. Siemens has released a new version for...
Siemens SIMATIC
View CSAF
Summary
SIMATIC S7-1500 devices contain a vulnerability that could allow an attacker to inject code by tricking a legitimate user into importing a specially...
Siemens SIDIS Prime
View CSAF
Summary
SIDIS Prime before V4.0.800 is affected by multiple vulnerabilities in the components OpenSSL, SQLite, and several Node.js packages as described below. Siemens has...
This rise of the splinternet? Data sovereignty risks and responses
We look at the political, legal and economic risks around data sovereignty, the fears for digital dependency and massive hyperscaler penetration in the UK...