Microsoft Defender triggered widespread false positive alerts after a faulty security update caused it to flag two legitimate DigiCert root certificates as malicious, potentially disrupting SSL/TLS validation and code-signing operations across enterprise environments worldwide.
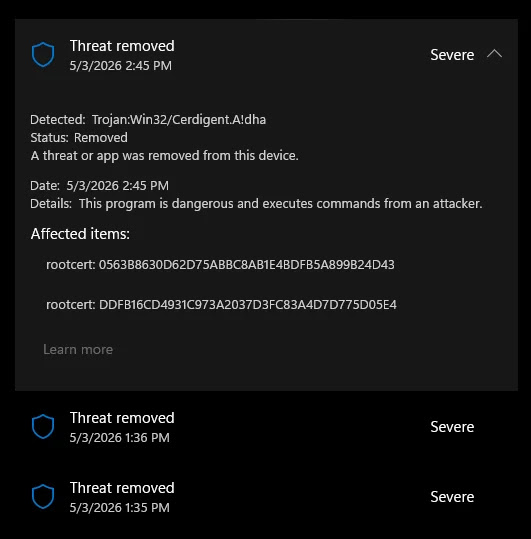
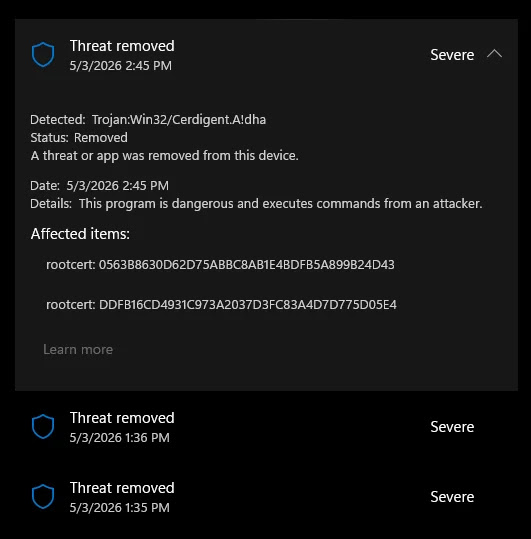
A Defender antimalware signature update released around April 30, 2026, introduced a detection labeled Trojan:Win32/Cerdigent.A!dha, which incorrectly identified registry entries belonging to two of the internet’s most widely trusted root certificates, DigiCert Assured ID Root CA (thumbprint: 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43) and DigiCert Trusted Root G4 (thumbprint: DDFB16CD4931C973A2037D3FC83A4D7D775D05E4) — as high-severity malware threats.
The certificates reside in the Windows trust store under the registry path HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates, where Windows manages trusted root and intermediate certificate authorities.
On affected systems, Microsoft Defender automatically quarantined the flagged certificate entries as part of its standard remediation workflow, effectively removing them from the Windows trust store.
This created a serious downstream risk: without these root certificates in place, systems could fail to validate SSL/TLS connections for websites and break code-signing verification for legitimate software, a scenario that could cascade into service disruptions, browser warnings, and application failures across enterprise networks.
Organizations relying on DigiCert-signed software or HTTPS endpoints were especially exposed.
Cybersecurity researcher Florian Roth (@cyb3rops) was among the first to publicly identify and amplify the issue, posting on X and urging the security community to investigate.
Roth shared an Advanced Hunting query to help administrators check whether the DigiCert certificates had been restored on affected devices:
text| where ActionType == "RegistryKeyCreated"
| where Timestamp > datetime(2026-05-03T04:00:00)
| project Timestamp, DeviceName, ActionType, InitiatingProcessFileName
| order by Timestamp desc
He also recommended a quick command-line check for affected systems: certutil -store AuthRoot | findstr -i "digicert" .
Microsoft’s own Q&A forums quickly filled with reports from administrators confirming the false positive, with users noting that the DigiCert certificate hashes matched officially published values from DigiCert’s website, confirming no actual compromise had occurred.
Microsoft’s Response
Microsoft acknowledged the issue and moved swiftly to roll out corrective definition updates, with version .430 cited as a key fix that began restoring the quarantined certificates on affected machines.
Security observers noted that the restoration appeared to be rolling out automatically across managed endpoints, suggesting Microsoft deployed a silent remediation alongside the corrected signature update.
Administrators in environments with restricted update policies were advised to manually verify the presence of certificates using certutil and to check the Advanced Hunting logs in Microsoft Defender for Endpoint to confirm the restoration.
This incident highlights the double-edged nature of automated threat remediation. While proactive quarantine protects against certificate-store tampering a known malware technique used to intercept TLS traffic or bypass security checks the same mechanism can cause significant operational harm when triggered incorrectly.
The Cerdigent false positive serves as a reminder that even trusted security platforms must maintain rigorous quality controls around signature releases, particularly for detections targeting foundational Windows infrastructure components like the root certificate trust store.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Microsoft Defender Mistakenly Flags DigiCert Root Certificates as Malware appeared first on Cyber Security News.