4 Months to Go: A New Year GDPR Checklist
As we enter the New Year, IT and security leaders have most likely been glued to revelations of major new CPU-level vulnerabilities Meltdown and...
Data Breaches Plague Organizations for Years
Once an organization’s network is breached, extinguishing the flames is just the first step in a long, painful and costly journey to recovery. There’s...
The Emerging Importance of Securing Access to AWS
With 50,000 attendees, over 1,000 breakout sessions and countless sponsors and exhibitors, the 2017 AWS re:Invent conference in Las Vegas was one of the...
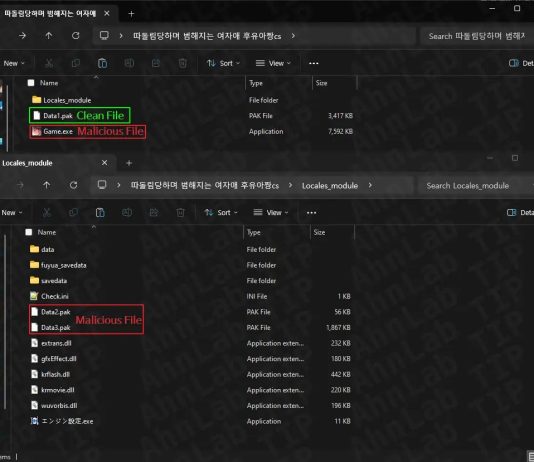
Skygofree: Following in the footsteps of HackingTeam
At the beginning of October 2017, we discovered new Android spyware with several features previously unseen in the wild. In the course of further...
Data Privacy Day
- Read more
Centrify Identity Services: Securing Docker and Containers
Introduction
We are excited to announce that Centrify now supports CoreOS Container Optimized Linux which several of our customers are using as part of their...
4 Steps to Reduce the Risk of Shared Account Passwords
Reduce the Risk of a Security Breach When Sharing Privileged Accounts
There are partners, employees, contractors, customers and others who access or try to access...
KLAS Findings on Healthcare DLP Strategies
KLAS Findings on Healthcare DLP Strategies
This webinar was recorded on December 19, 2017.
- Read more
Centrify Predicts: Cybersecurity in 2018
As we start 2018, we have continued to see major breaches across industries, only last year we witnessed at least two companies — Uber...
The Year in Review: Centrify Builds Momentum
The Centrify solution made great strides in 2017, chronicled in Part I of this blog. Product enhancements, combined with the market’s growing understanding of...