2025 Advanced Persistent Bot Report: Scraper Bots Deep-Dive
How much do scraper bots affect your industry? - Read more
Prevent Web Scraping by Applying the Pyramid of Pain
The Bots Pyramid of Pain: a framework for effective bot defense. - Read more
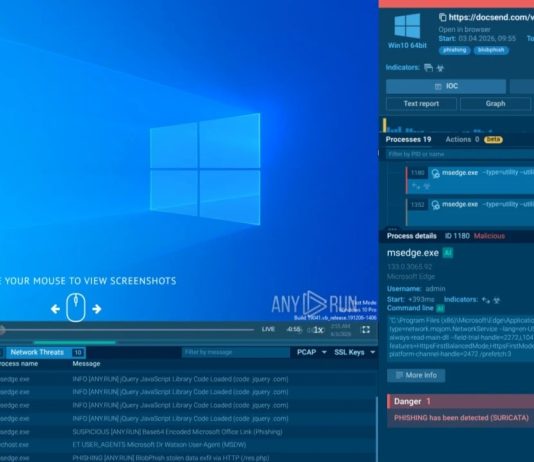
2025 Advanced Persistent Bots Report
Uncovering the true scale of persistent bot activity, and the advanced techniques that bot operators use in order to remain hidden from bot defenses....
Analyzing the Global Increase in Vulnerability Scanning in 2024
BotPoke comes to the foreground yet again. - Read more
Ten Years of Let’s Encrypt: Announcing support from Jeff Atwood
As we touched on in our first blog post highlighting ten years of Let’s Encrypt: Just as remarkable to us as the technical innovations...
Why Critical MongoDB Library Flaws Won’t See Mass Exploitation
Discover how to mitigate CVE-2024-53900 and CVE-2025-23061, which expose Node.js APIs to remote attacks. - Read more
Understanding data mesh in public sector: Pillars, architecture, and examples
Discover how Elastic enables data mesh in the public sector with key pillars, architecture, and real-world examples for better data access and governance. -...
Enterprises Should Consider Replacing Employees’ Home TP-Link Routers
An examination of CVE trends from February 2025 scanning data. - Read more
Elastic achieves AWS Government ISV Partner Competency, strengthening public sector solutions portfolio
Elastic has earned the AWS Government ISV Partner Competency. This recognition validates Elastic's expertise in delivering Search AI solutions that help government agencies modernize...
We Issued Our First Six Day Cert
Earlier this year we announced our intention to introduce short-lived certificates with lifetimes of six days as an option for our subscribers. Yesterday we...