Saudi Arabia ordered to pay £3m to UK dissident targeted with Pegasus spyware
A court has found that the Kingdom of Saudi Arabia subjected a London-based human rights activist to abuse and physical violence after infecting his...
HoneyMyte updates CoolClient and deploys multiple stealers in recent campaigns
Over the past few years, we’ve been observing and monitoring the espionage activities of HoneyMyte (aka Mustang Panda or Bronze President) within Asia and...
SoundCloud – 29,815,722 breached accounts
In December 2025, SoundCloud announced it had discovered unauthorised activity on its platform. The incident allowed an attacker to map publicly available SoundCloud profile...
OpenSSL January 2026 Security Update: CMS and PKCS#12 Buffer Overflows
A deep dive into OpenSSL’s January 2026 CMS and PKCS#12 vulnerabilities, including a pre-auth stack overflow and a PKCS#12 parsing bug. - Read...
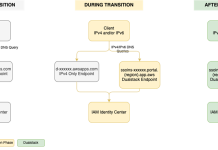
IAM Identity Center now supports IPv6
Amazon Web Services (AWS) recommends using AWS IAM Identity Center to provide your workforce access to AWS managed applications—such as Amazon Q Developer—and AWS...
Russian hackers accused of attack on Poland electricity grid
On Dec. 29 and 30, the Polish electricity grid was subjected to a cyberattack that nearly knocked out power to...
Best VPN Services of 2026: Fast, Secure & Affordable
In today’s digital world, online privacy and security have never been more important. With cybercrime on the rise and government surveillance becoming more...
eScan Antivirus Supply Chain Breach Delivers Signed Malware
Supply chain breach in eScan antivirus distributes multi-stage malware via legitimate updates - Read more
Updated PCI PIN compliance package for AWS CloudHSM now available
Amazon Web Services (AWS) is pleased to announce the successful completion of Payment Card Industry Personal Identification Number (PCI PIN) audit for...
Microsoft Shared BitLocker Keys With FBI, Raising Privacy Fears
Microsoft confirmed it can hand over BitLocker recovery keys stored in the cloud under warrant, reviving debate over who controls encrypted data.
The post Microsoft...