A mining multitool
Recently, an interesting miner implementation appeared on Kaspersky Lab’s radar. The malware, which we dubbed PowerGhost, is capable of stealthily establishing itself in a...
A study of car sharing apps
The growing popularity of car sharing services has led some experts to predict an end to private car ownership in big cities. The statistics...
Calisto Trojan for macOS
An interesting aspect of studying a particular piece of malware is tracing its evolution and observing how the creators gradually add new monetization or...
The return of Fantomas, or how we deciphered Cryakl
In early February this year, Belgian police seized the C&C servers of the infamous Cryakl cryptor. Soon afterwards, they handed over the private keys...
Coinvault, the court case
Today, after almost 3 years of waiting, it was finally the day of the trial. In the Netherlands, where the whole case took place,...
APT Trends Report Q2 2018
In the second quarter of 2017, Kaspersky Lab’s Global Research and Analysis Team (GReAT) began publishing summaries of the quarter’s private threat intelligence reports,...
To crypt, or to mine – that is the question
Way back in 2013 our malware analysts spotted the first malicious samples related to the Trojan-Ransom.Win32.Rakhni family. That was the starting point for this...
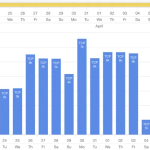
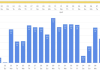
Ransomware and malicious crypto miners in 2016-2018
Ransomware is not an unfamiliar threat. For the last few years it has been affecting the world of cybersecurity, infecting and blocking access to...
Pbot: evolving adware
The adware PBot (PythonBot) got its name because its core modules are written in Python. It was more than a year ago that we...
Modern OSs for embedded systems
At Kaspersky Lab we analyze the technologies available on cybersecurity market and this time we decided to look at what OS developers are offering...