Olympic Destroyer is still alive
In March 2018 we published our research on Olympic Destroyer, an advanced threat actor that hit organizers, suppliers and partners of the Winter Olympic...
LuckyMouse hits national data center to organize country-level waterholing campaign
What happened?
In March 2018 we detected an ongoing campaign targeting a national data center in the Central Asia that we believe has been active...
A MitM extension for Chrome
Browser extensions make our lives easier: they hide obtrusive advertising, translate text, help us choose in online stores, etc. There are also less desirable...
FIFA public Wi-Fi guide: which host cities have the most secure networks?
We all know how easy it is for users to connect to open Wi-Fi networks in public places. Well, it is equally straightforward for...
Netkids
Children today are completely at home in the digital space. They use digital diaries and textbooks at school, communicate via instant messaging, play games...
Trojan watch
We continue to research how proliferation of IoT devices affects the daily lives of users and their information security. In our previous study, we...
VPNFilter EXIF to C2 mechanism analysed
On May 23 2018, our colleagues from Cisco Talos published their excellent analysis of VPNFilter, an IoT / router malware which exhibits some worrying...
Backdoors in D-Link’s backyard
“If you want to change the world, start with yourself.” In the case of security research this can be rephrased to: “If you want...
Roaming Mantis dabbles in mining and phishing multilingually
In April 2018, Kaspersky Lab published a blogpost titled ‘Roaming Mantis uses DNS hijacking to infect Android smartphones’. Roaming Mantis uses Android malware which...
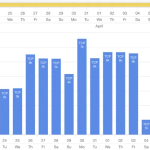
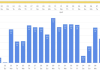
IT threat evolution Q1 2018. Statistics
Q1 figures
According to KSN:
Kaspersky Lab solutions blocked 796,806,112 attacks launched from online resources located in 194 countries across the globe.
282,807,433 unique URLs were...