We know what your kids did this summer
For many kids and teenagers, summer is all about ditching school books in favor of hobbies and fun. Every year we release a report...
What are botnets downloading?
Spam mailshots with links to malware and bots downloading other malware are just a couple of botnet deployment scenarios. The choice of infectious payload...
Loki Bot: On a hunt for corporate passwords
Starting from early July, we have seen malicious spam activity that has targeted corporate mailboxes. The messages discovered so far contain an attachment with...
Operation AppleJeus: Lazarus hits cryptocurrency exchange with fake installer and macOS malware
Overview
Lazarus has been a major threat actor in the APT arena for several years. Alongside goals like cyberespionage and cybersabotage, the attacker has been...
Dark Tequila Añejo
Dark Tequila is a complex malicious campaign targeting Mexican users, with the primary purpose of stealing financial information, as well as login credentials to...
Security assessment of corporate information systems in 2017
Each year, Kaspersky Lab’s Security Services department carries out dozens of cybersecurity assessment projects for companies worldwide. In this publication, we present a general...
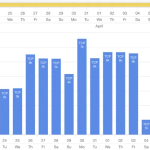
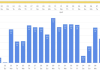
Spam and phishing in Q2 2018
Quarterly highlights
GDPR as a phishing opportunity
In the first quarter, we discussed spam designed to exploit GDPR (General Data Protection Regulation), which came into effect...
IT threat evolution Q2 2018
Targeted attacks and malware campaigns
Operation Parliament
In April, we reported the workings of Operation Parliament, a cyber-espionage campaign aimed at high-profile legislative, executive and judicial...
IT threat evolution Q2 2018. Statistics
Q2 figures
According to KSN:
Kaspersky Lab solutions blocked 962,947,023 attacks launched from online resources located in 187 countries across the globe.
351,913,075 unique URLs were...
How do file partner programs work?
It’s easy to notice if you’ve fallen victim to an advertising partner program: the system has new apps that you didn’t install, ad pages...