Patched Facebook Vulnerability Could Have Exposed Private Information About You and Your Friends
In a previous blog we highlighted a vulnerability in Chrome that allowed bad actors to steal Facebook users’ personal information; and, while digging around...
New Docker-based Dev Pipeline: Microservice Projects Just Got A ‘Speed-Boost’
A bulwark of software engineering projects, the development pipeline is an automated process used to deliver changes from development through to production; enabling near...
New Imperva Java SDK: Greasing The Wheels for Active Directory Coding Projects
According to StackOverflow’s 2018 Developer Survey, Java remains one of the world’s most popular coding languages, universally liked for its versatility and ease of...
44% of Security Professionals Spend More than 20 Hours a Week Responding to Alerts
As the global cybersecurity climate continues to heat up, so too do the subsequent levels of alert fatigue IT security professionals have to deal...
Survey: 44% of Security Professionals Spend More than 20 Hours a Week Responding to...
As the global cybersecurity climate continues to heat up, so too do the subsequent levels of alert fatigue IT security professionals have to deal...
Read: How To Build Resilient Cloud Configuration Shields
Configurable systems have a high level of flexibility and are better adapted to most customer needs, but their management isn’t a trivial task in...
The World’s Most Popular Coding Language Happens to be Most Hackers’ Weapon of Choice
Python will soon be the world’s most prevalent coding language.
That’s quite a statement, but if you look at its simplicity, flexibility and the...
Imperva Joins Global Cybersecurity Tech Accord
Imperva is dedicated to the global fight to keep people’s data and applications safe from cybercriminals. What this means for our Imperva Threat Research...
Microsoft and Imperva Collaboration Bolsters Data Compliance and Security Capabilities
This article explains how Imperva SecureSphere V13.2 has leveraged the latest Microsoft EventHub enhancements to help customers maintain compliance and security controls as regulated...
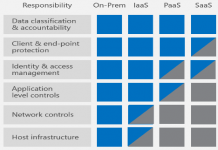
Explainer Series: RDaaS Security and Managing Compliance Through Database Audit and Monitoring Controls
As organizations move to cloud database platforms they shouldn’t forget that data security and compliance requirements remain an obligation. This article explains how you...