Enhance Imperva Cloud WAF with a New Management Tool in the Imperva GitHub
Imperva recently launched the Imperva GitHub where our global community can access tools, code repositories and other neat resources that aid collaboration and streamline...
Imperva Cloud WAF and Graylog, Part II: How to Collect and Ingest SIEM Logs
This guide gives step-by-step guidance on how to collect and parse Imperva Cloud Web Application Firewall (WAF, formerly Incapsula) logs into the Graylog SIEM...
Now-Patched Google Photos Vulnerability Let Hackers Track Your Friends and Location History
A now-patched vulnerability in the web version of Google Photos allowed malicious websites to expose where, when, and with whom your photos were taken.
Background
One...
How Our Threat Analytics Multi-Region Data Lake on AWS Stores More, Slashes Costs
Data is the lifeblood of digital businesses, and a key competitive advantage. The question is: how can you store your data cost-efficiently, access it...
Mapping Communication Between Facebook Accounts Using a Browser-Based Side Channel Attack
A now-patched vulnerability in the web version of Facebook Messenger allowed any website to expose who you have been messaging with.
In a previous post,...
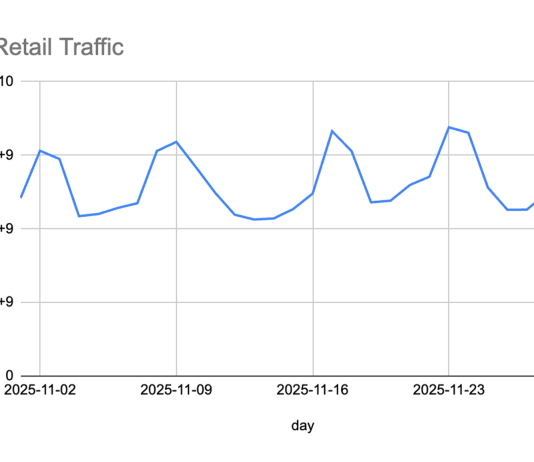
Hundreds of Vulnerable Docker Hosts Exploited by Cryptocurrency Miners
Docker is a technology that allows you to perform operating system level virtualization. An incredible number of companies and production hosts are running Docker...
Don’t Let Security Needs Halt Your Digital Transformation. Imperva FlexProtect Offers Agile Security for...
Is your enterprise in the midst of a digital transformation? Of course it is. Doing business in today’s global marketplace is more competitive than...
Latest Drupal RCE Flaw Used by Cryptocurrency Miners and Other Attackers
Another remote code execution vulnerability has been revealed in Drupal, the popular open-source Web content management system. One exploit — still working at time...
No One is Safe: the Five Most Popular Social Engineering Attacks Against Your Company’s...
Your Wi-Fi routers and access points all have strong WPA2 passwords, unique SSIDs, the latest firmware updates, and even MAC address filtering. Good job,...
How Imperva’s New Attack Crowdsourcing Secures Your Business’s Applications
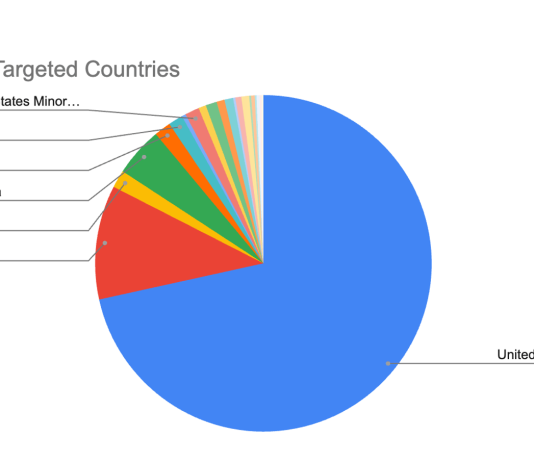
Attacks on applications can be divided into two types: targeted attacks and “spray and pray” attacks. Targeted attacks require planning and usually include a...