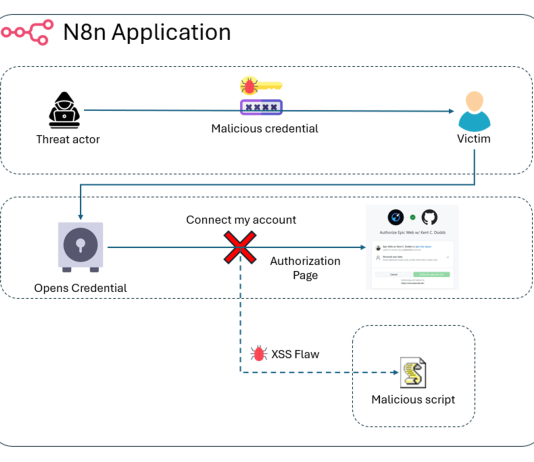
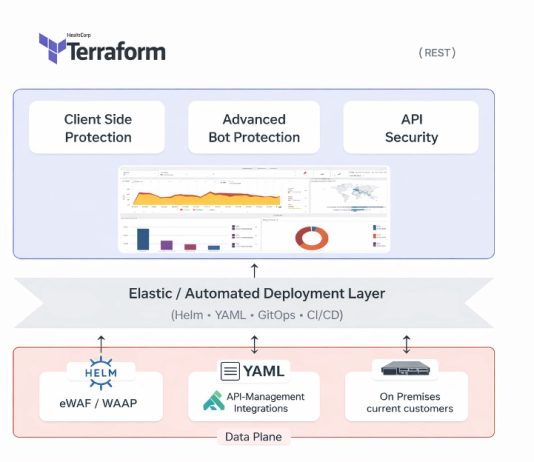
Security Strategies for DevOps, APIs, Containers and Microservices
More and more IT professionals see DevSecOps, a practice which integrates security measures earlier in the development process to improve production code quality, as...
Cloud Database Migration Peer Insights [Report]
Not long ago, for security, compliance or other reasons, it was unthinkable for many regulated organizations to move sensitive data into the cloud. It’s...
Cloud Migration Fundamentals
The advantages offered by a cloud-based environment make it an easy decision for most companies to make. Still, there are numerous critical choices to...
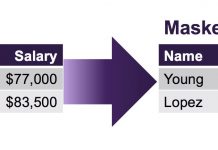
Three Reasons Why GDPR Encourages Pseudonymization
The General Data Protection Regulation (GDPR) is the European Union’s new data regulation designed to provide individuals with rights and protections over their personal...
Women in Tech and Career Spotlight: Jerusalem Bicha
We conclude our series featuring women in tech at Imperva with an interview with Jerusalem Bicha, network operations team lead at Imperva. We talked...

![Cloud Database Migration Peer Insights [Report]](https://www.dataproof.co.za/wp-content/uploads/2018/01/cloud-database-migration-peer-insights-report-218x150.png)