The Meta 2FA Trap: From Verified Badge to Account Takeover
By: Cole Adkins Cofense Phishing Defense CenterMeta, the parent company of platforms such as Facebook and Instagram, plays a major role in both personal...
Udemy – 1,401,259 breached accounts
In April 2026, online training company Udemy was the victim of a “pay or leak” extortion attempt perpetrated by the ShinyHunters group. The data...
73 Open VSX Sleeper Extensions Linked to GlassWorm Activate New Malware Campaign
The GlassWorm supply chain attack targeting the Open VSX marketplace has escalated with the discovery of 73 new “sleeper” extensions. Identified in April 2026,...
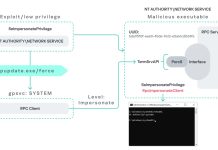
New Windows RPC Vulnerability Lets Attackers Escalate Privileges Across All Windows Versions
PhantomRPC, a newly identified architectural vulnerability in Windows Remote Procedure Call (RPC) that enables local privilege escalation to SYSTEM-level access, potentially affecting every version...
CVE-2026-23442 ipv6: add NULL checks for idev in SRv6 paths
Information published. - Read more
Metasploit Wrap-Up 04/25/2026
Check Method VisibilityMetasploit has supported check methods for many years now. It’s not always desirable to jump straight into exploiting a vulnerability but instead...
New US House privacy bills raise hard questions about enterprise data collection
US House Republicans have introduced two major privacy proposals that would reshape how US companies collect, process, and retain consumer...
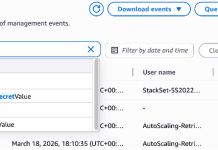
Protecting your secrets from tomorrow’s quantum risks
As outlined in the AWS post-quantum cryptography (PQC) migration plan, addressing the risk of harvest now, decrypt later (HNDL) attack is an...
Scattered Spider co-conspirator pleads guilty
Another member of the notorious Scattered Spider gang of cyber criminals has pleaded guilty in a US court, and will...