Dragonica Lunaris – 126,293 breached accounts
In December 2025, the European Dragonica private server Dragonica Lunaris suffered a data breach. The incident exposed 126k email addresses, usernames, dates of birth...
Windows93 / Myspace93 – 46,105 breached accounts
In January 2021, the parody site Windows93 suffered a data breach of the Myspace93 sub-site after a beta application was exploited to download server...
The Vulnerability Flood Is Now a Board Conversation. Here’s How to Lead It.
I've had some version of the same conversation dozens of times since Mythos and Daybreak emerged. CISOs want to know how worried they...
Unpatchable Vulnerabilities of Kubernetes: CVE-2021-25740
A look at how Kubernetes CVE-2021-25740 allows users with EndpointSlice access to redirect traffic via shared ingress and load balancer services. - Read...
The data platform bet: Why financial AI initiatives stall and how the winners scale
Discover why 40% of financial AI initiatives fail, and learn how a unified data platform enables secure, real-time AI scaling in regulated environments. -...
Microsoft Disrupts Malware-Signing Service Used by Ransomware Gangs
Microsoft disrupted Fox Tempest, a malware-signing service accused of abusing Azure certificates to disguise ransomware and malware as trusted software.
The post Microsoft Disrupts Malware-Signing...
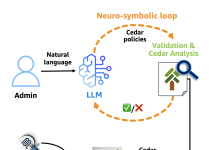
Why Policy in Amazon Bedrock AgentCore chose Cedar for securing agentic workflows
Agents have agency: they adapt and find multiple ways to solve problems. This autonomy creates a fundamental security challenge: the large language model (LLM)...
AWS Security Hub Extended: Why enterprise security products should sell themselves
Our largest security services customers started the same way every customer does – with a click. They enabled Amazon GuardDuty, Amazon Inspector,...
Spanish police ‘systematically’ hid cryptophone intercepts from courts, claims ex chief
Former Spanish police chief, on trial for drug trafficking, claims UK and Colombian police assisted in creating fictitious intelligence reports to hide use of...