The Complete Guide to Container Security
The Complete Guide to Container Security #outlook a{ padding:0; } body{ width:100% !important; } .ReadMsgBody{ width:100%; } .ExternalClass{ width:100%; } body{ -webkit-text-size-adjust:none; } body{ margin:0; padding:0; } img{ border:0; height:auto; line-height:100%; outline:none; text-decoration:none; } table td{ border-collapse:collapse; } #backgroundTable{ height:100% !important; margin:0; padding:0; width:100% !important; } body,#backgroundTable{...
It’s Time for Managers to Lead Security by Example, Not Blame Younger Workers
The age gap is something that all organisations over the years have had to deal with in one way or another. But the flood of consumer-grade technologies into the workplace in recent years has arguably widened that gap even further.
To learn more, Centrify recently polled not only 1,000 UK office workers aged 18-24 but also 500 senior decision makers....
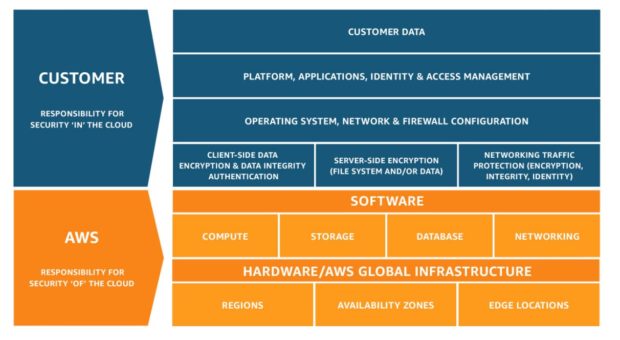
Cloud Migration Fundamentals: Overcoming Barriers to App Security [Infographic]
As more organizations move to the cloud, the line of responsibility in securing applications can become rather blurred.
The concept of control has historically rested in physical location and ownership. With the move to the cloud, however, the idea of security by proxy is changing and so should our approach.
First things first though, how do we meet the challenges that...
Ransomware and malicious crypto miners in 2016-2018
Ransomware is not an unfamiliar threat. For the last few years it has been affecting the world of cybersecurity, infecting and blocking access to various devices or files and requiring users to pay a ransom (usually in Bitcoins or another widely used e-currency), if they want to regain access to their files and devices.
The term ransomware covers two main...
Achieve CIS Benchmarks for Cloud, Container and DevOps Environments
Achieve CIS Benchmarks for Cloud, Container and DevOps Environments #outlook a{ padding:0; } body{ width:100% !important; } .ReadMsgBody{ width:100%; } .ExternalClass{ width:100%; } body{ -webkit-text-size-adjust:none; } body{ margin:0; padding:0; } img{ border:0; height:auto; line-height:100%; outline:none; text-decoration:none; } table td{ border-collapse:collapse; } #backgroundTable{ height:100% !important; margin:0; padding:0; width:100%...
Black Hat 2018
<img src="/sites/default/files/Blackhat-logo.png">
Join Digital Guardian at Black Hat 2018!
- Read more
Making Smarter Access Control Decisions
Hey Siri, block that attacker, please
Wouldn’t it be great if Siri, Alexa, or Google Assistant had the intelligence to figure out malicious intent, govern access to our sensitive corporate data, and alert us in real time when something dodgy was going on? Well, they do leverage modern machine learning and AI to make “intelligent” decisions, but they’re clearly not...
Pbot: evolving adware
The adware PBot (PythonBot) got its name because its core modules are written in Python. It was more than a year ago that we detected the first member of this family. Since then, we have encountered several modifications of the program, one of which went beyond adware by installing and running a hidden miner on victim computers:
Miner code installed...
Zero Trust Security and DevOps Take the Crown at AWS Public Sector Summit 2018
Last week, Amazon Web Services hosted its AWS Public Sector Summit in Washington, DC. In its 9th year, the event attracted thousands of global leaders and IT security practitioners from government, education, and non-profit organizations to learn how to start their path to the cloud or how to maintain momentum once they’ve begun the transformation.
BULLISH OUTLOOK FOR CLOUD ADOPTION...



![Cloud Migration Fundamentals: Overcoming Barriers to App Security [Infographic]](http://www.dataproof.co.za/wp-content/uploads/2018/07/cloud-migration-fundamentals-overcoming-barriers-to-app-security-infographic-696x435.png)