Cyber Security Report 2026
Check Point Research continuously investigates real-world attacks, vulnerabilities, attackers’ infrastructure, and emerging techniques across global networks and environments. The Cyber Security Report 2026 consolidates...
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard Tenable Research has identified and responsibly disclosed a data exfiltration vulnerability in...
Trusted, Signed, Still Malicious. Exploiting Custom Email Text to Bypass Security Controls
By: Kahng An, Intelligence TeamA recent series of phone scam emails has been able to bypass traditional email security measures by placing malicious messages...
Phishing at Cloud Scale: How AWS is Abused for Credential Theft
Threat actors are abusing web services from Amazon like Simple Storage Service (S3) buckets, Amazon Simple Email Service (SES), and Amazon Web Service (AWS)...
How Elastic Support uses AI to deliver faster, expert-verified solutions
We use AI and RAG to accelerate answers — not replace experts. Every response is reviewed, validated, and refined by engineers to ensure accurate,...
[R1] Tenable Network Monitor Version 6.5.3 Fixes Multiple Vulnerabilities
Tenable Network Monitor Version 6.5.3 Fixes Multiple Vulnerabilities Arnie Cabral Tue, 01/27/2026 - 14:02
Nessus Network Monitor leverages third-party software to help provide...
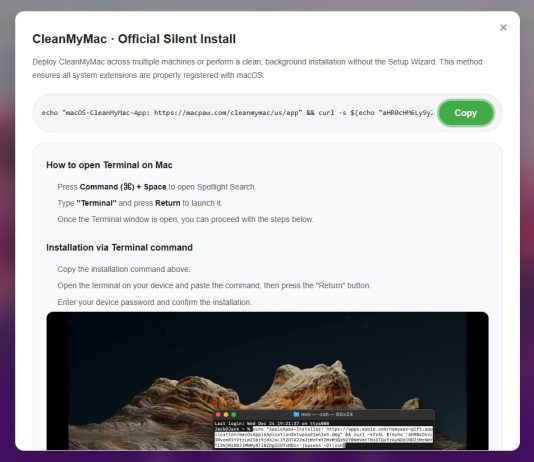
File integrity monitoring with AWS Systems Manager and Amazon Security Lake
Customers need solutions to track inventory data such as files and software across Amazon Elastic Compute Cloud (Amazon EC2) instances, detect unauthorized...
Wave of ShinyHunters vishing attacks spreading fast
The ShinyHunters hacking collective that caused chaos in 2025 is ramping up a new voice phishing campaign, with several potential victims already identified ...
Johnson Controls Products
View CSAF
Summary
Successful exploitation of this vulnerability could result in remote SQL execution, leading to alteration or loss of data.
The following versions of Johnson Controls...