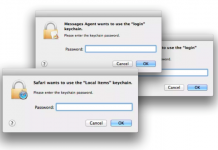
Sync Your Jaws Into Mac Keychain
“Well this is not a boat accident! It wasn’t any propeller! It wasn’t any coral reef! And it wasn’t Jack the Ripper! It was...
VPNFilter EXIF to C2 mechanism analysed
On May 23 2018, our colleagues from Cisco Talos published their excellent analysis of VPNFilter, an IoT / router malware which exhibits some worrying...
It’s Almost GDPR D-Day: So What Happens Next?
Over the past 12 months during this blog series I’ve tried to provide insight into some of the key aspects of the GDPR and...
Backdoors in D-Link’s backyard
“If you want to change the world, start with yourself.” In the case of security research this can be rephrased to: “If you want...
Centrify Does it Again – Innovative Security Analytics Integration with Palo Alto Networks App...
Centrify and Palo Alto Networks have announced another important integration that can help customers quickly and decisively discover anomalies that are a security threat.
Building...
Roaming Mantis dabbles in mining and phishing multilingually
In April 2018, Kaspersky Lab published a blogpost titled ‘Roaming Mantis uses DNS hijacking to infect Android smartphones’. Roaming Mantis uses Android malware which...
Analyst Insights – Building An Efficient Data Security Program with Forrester
Analyst Insights – Building An Efficient Data Security Program
This webinar was recorded on May 17, 2018.
- Read more
Centrify and SailPoint Join Forces to Apply Zero Trust Security Best Practices to Identity...
Today, Centrify is proud to announce the integration of the Centrify Privileged Access Service with SailPoint® Technologies IdentityIQ solution.
This integration provides joint customers with...










![[VitalQIP Migration Series] Part 1: Three Reasons Why VitalQIP Migration Should Be on Your Radar](https://www.dataproof.co.za/wp-content/uploads/2018/05/vitalqip-migration-series-part-1-three-reasons-why-vitalqip-migration-should-be-on-your-radar-218x150.jpg)










