When your DDoS mitigation provider goes down: Why traffic control can’t be outsourced
Since the headline-grabbing outages of 2021, we’ve had recurring conversations with large enterprises asking some version of the same question.
Do we really want our...
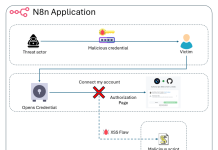
N8N: Shared Credentials and Account Takeover
Executive Summary
We identified a security weakness in n8n’s credential management layer that could have completely compromised the application’s security. This finding highlights the core...
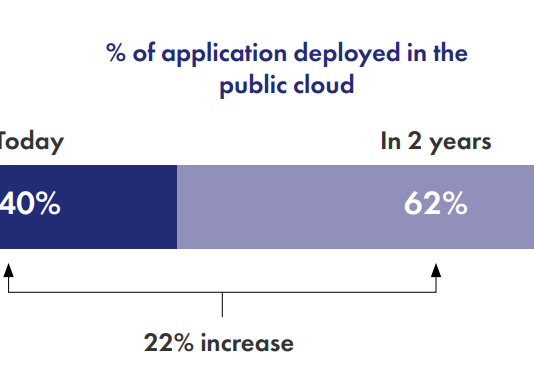
Integrating Advanced API Security with Imperva Gateway Environment
As APIs power the majority of modern web applications, implementing robust API security is no longer optional – it’s a critical necessity for data...
Cloud Based WAF Upload Scan and Control: The New Standard for File Upload Security
We’re excited to announce the launch of Upload Scan and Control, an essential new feature for Imperva Cloud WAF. This add-on tackles one of...
A New Denial-of-Service Vector in React Server Components
React Server Components (RSC) have introduced a hybrid execution model that expands application capabilities while increasing the potential attack surface.
Following earlier disclosures and fixes...
Imperva Customers Protected Against CVE-2026-21962 in Oracle HTTP and WebLogic
What Is CVE-2026-21962?
CVE-2026-21962 is a critical (CVSS 10.0) vulnerability in the Oracle HTTP Server and the WebLogic Server Proxy Plug-in for Apache HTTP Server...
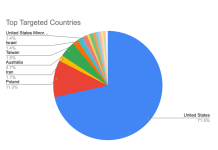
Black Friday 2025 in Review: What Retailers Need to Know About This Year’s Holiday...
Holiday shopping season is in full swing, and Black Friday 2025 continued to demonstrate that consumer demand and attacker activity shows no signs of...
Security by Design: Why Multi-Factor Authentication Matters More Than Ever
In an era marked by escalating cyber threats and evolving risk landscapes, organisations face mounting pressure to strengthen their security posture whilst maintaining seamless...
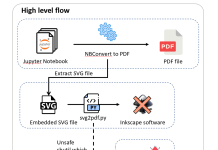
Code Execution in Jupyter Notebook Exports
After our research on Cursor, in the context of developer-ecosystem security, we turn our attention to the Jupyter ecosystem. We expose security risks we...
Imperva Partners with TollBit to Power AI Traffic Monetization for Content Owners
The surge in AI-driven traffic is transforming how websites manage their content. With AI bots and agents visiting sites at unprecedented rates (often scraping...