Threat Intelligence Automation
Key Takeaways Real-time intelligence at scale: Threat intelligence automation accelerates detection and response by processing vast threat data instantly, far faster than...
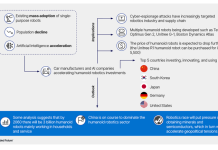
The Future of Humanoid Robotics
Summary Advances in large-language models (LLMs) and the anticipated arrival of artificial general intelligence (AGI) are rapidly closing the gap between concept and...
Analysis of a Large-Scale DDoS Attack Against a Payment Processing Platform
The two-wave attack reached a peak of 1.8 Tbps. - Read more
The 6 URL Shorteners You Didn’t Know Were Helping Hackers
By: Madalynn Carr, Intelligence TeamThreat actors are constantly evolving and adapting by discovering new, unique ways to bypass email-based security controls. One key method...
Operational Cyber Threat Intelligence
Key Takeaways The average organization today relies on multiple platforms and tools delivering round-the-clock feeds of security information and alerts. Under this...
Addressing the vulnerability prioritization challenge
How do you prioritize what vulnerabilities to patch when you have thousands of alerts and critical remote code execution flaws buried next to...
Personal details of Tate galleries job applicants leaked online
Sensitive information relates to more than 100 individuals and their refereesPersonal details submitted by applicants for a job at Tate art galleries have been...
Akira Ransomware
FortiGuard Labs continue to observe detections in the wild related to the Akira ransomware group. According to the new report by CISA it has...
A 2025 look at real-world Kubernetes version adoption
A 2025 look at real-world Kubernetes version adoption - Read more
Celebrating partner excellence: The 2025–2026 Elastic Partner Awards
The Elastic Partner Awards honor partners for driving customer impact through innovation, AI, and cloud adoption. Follow this blog for updates as winners are...