UAT-9686 actively targets Cisco Secure Email Gateway and Secure Email and Web Manager
Cisco Talos recently discovered a campaign targeting Cisco AsyncOS Software for Cisco Secure Email Gateway, formerly known as Cisco Email Security Appliance (ESA), and...
GachiLoader: Defeating Node.js Malware with API Tracing
Research by: Sven Rath (@eversinc33), Jaromír Hořejší (@JaromirHorejsi) Key Points
The YouTube Ghost Network is a malware distribution network that uses compromised accounts to promote malicious videos and spread...
Lexi DiScola’s guide to global teamwork and overflowing TBRs
Welcome back to Humans of Talos. This month, Amy chats with Senior Cyber Threat Analyst Lexi DiScola from the Strategic Analysis team. Lexi’s journey...
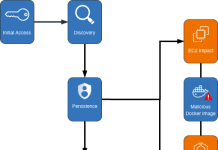
Windows Persistence Explained: Techniques, Risks, and What Defenders Should Know
By: Kahng An, Intelligence TeamModern Windows systems include many built-in features that help applications run smoothly and support everyday user activity. Unfortunately, many of...
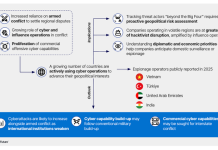
Cyber on the Geopolitical, Battlefield: Beyond the, “Big Fourˮ
Executive Summary Regional conflicts and weakened international institutions are driving the use of offensive cyber operations beyond the “Big Four” (China, Russia, Iran,...
BlueDelta’s Persistent Campaign Against UKR.NET
The analysis cut-off date for this report was July 30, 2025 Executive Summary Between June 2024 and April 2025, Recorded Future’s Insikt Group...
Introducing Pathfinding.cloud
Introducing Pathfinding.cloud, a library of AWS IAM privilege escalation paths - Read more
The $0 Transaction That Signaled a Nation-State Cyberattack
Key Points: Fraud enables cyber operations: Threat actors used compromised payment cards validated through Chinese-operated card-testing services to attempt...
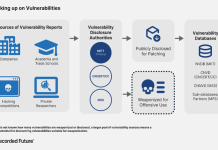
China’s Zero-Day Pipeline: From Discovery to Deployment
Executive Summary China’s observed use of zero-days has declined since 2023. However, it has expanded its capacity to discover and manage vulnerabilities,...
GuardDuty Extended Threat Detection uncovers cryptomining campaign on Amazon EC2 and Amazon ECS
Amazon GuardDuty and our automated security monitoring systems identified an ongoing cryptocurrency (crypto) mining campaign beginning on November 2, 2025. The operation...