Elastic wins fifth Google Cloud Partner of the Year award
For the fifth time, Elastic has been recognized for its achievements in the Google Cloud ecosystem, helping joint customers deploy generative AI solutions in...
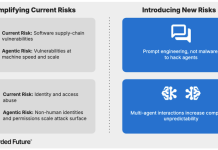
Emerging Enterprise Security Risks of AI
Summary Agentic AI adoption is accelerating rapidly as enterprise software and applications increasingly incorporate task-specific AI agents, enabling autonomous execution of complex tasks...
This VPN Lets You Verify Your Business Privacy For $130
VP.NET makes VPN privacy verifiable, not just policy-based, with secure enclave tech for up to five devices.
The post This VPN Lets You Verify Your...
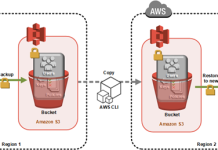
How to clone an AWS CloudHSM cluster across Regions
Important: As of January 1, 2025, Client SDK 3 tools (CMU and KMU) are no longer supported. This guide has been...
Flowise – Path Traversal in Vector Store basePath
Flowise - Path Traversal in Vector Store basePath The Faiss and SimpleStore (LlamaIndex) vector store implementations accept a basePath parameter from user-controlled input and...
Flowise – Cypher Injection in GraphCypherQAChain
Flowise - Cypher Injection in GraphCypherQAChain The GraphCypherQAChain node forwards user-provided input directly into the Cypher query execution pipeline without proper sanitization. An attacker...
Flowise – Missing Authentication on NVIDIA NIM Endpoints
Flowise - Missing Authentication on NVIDIA NIM Endpoints The NVIDIA NIM router (/api/v1/nvidia-nim/*) is whitelisted in the global authentication middleware, allowing unauthenticated access to...
20th April – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 20th April, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
Booking.com, the Amsterdam-based...
DFIR Report – The Gentlemen & SystemBC: A Sneak Peek Behind the Proxy
Key Points
The Gentlemen ransomware‑as‑a‑service (RaaS) program is rapidly gaining popularity, attracting numerous affiliates and publicly claiming over 320 victims, with the majority of attacks (240)...