Ivanti patches two actively exploited critical vulnerabilities in EPMM
IT software company Ivanti released patches for its Endpoint Manager Mobile (EPMM) product to fix two new remote code execution...
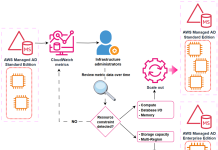
Explore scaling options for AWS Directory Service for Microsoft Active Directory
You can use AWS Directory Service for Microsoft Active Directory as your primary Active Directory Forest for hosting your users’ identities. Your...
SoundCloud Data Breach Exposes Nearly 30M User Accounts
A SoundCloud breach affecting 29.8 million accounts exposed email addresses and profile data, increasing phishing risks.
The post SoundCloud Data Breach Exposes Nearly 30M User...
Labyrinth Chollima Evolves into Three North Korean Hacking Groups
CrowdStrike assessed that two new threat actor groups have spun off from North Korean Labyrinth Chollima hackers - Read more
New AI-Developed Malware Campaign Targets Iranian Protests
The RedKitten campaign distributes lures designed to target people seeking information about missing persons or political dissidents in Iran - Read more
Chromium: CVE-2026-1504 Inappropriate implementation in Background Fetch API
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2024 ) for more information. -...
Context engineering: The missing layer for trusted AI in financial services
AI in financial services breaks down without trusted context. Discover how context engineering enables real-time, explainable, and compliant AI and how Elastic powers fraud...
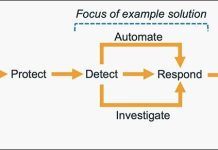
How to get started with security response automation on AWS
At AWS, we encourage you to use automation. Not just to deploy your workloads and configure services, but to also help you quickly detect...
I’m locked in!
Welcome to this week’s edition of the Threat Source newsletter.I’ve struggled a lot over the last few years with balance. I want to follow the...