Punchbowl Phishing Attack Explained: How Digital Invites Are Used to Steal Credentials
By: Adriane Andaya, Cofense Phishing Defense CenterIn today's digital age, receiving online invitations to events has become commonplace. Sending and receiving invites has never...
Preparing for Russia’s New Generation Warfare in Europe
Executive Summary Since its full-scale invasion of Ukraine in February 2022, Russia has waged what we assess is largely opportunistic, though increasingly aggressive,...
Shorter Certificate Lifetimes and Rate Limits
As previously announced, over the next two years we will be switching the default certificate lifetime from 90 days to 64 days, and then...
January 2026 CVE Landscape: 23 Critical Vulnerabilities Mark 5% Increase, APT28 Exploits Microsoft Office...
January 2026 saw a modest 5% increase in high-impact vulnerabilities, with Recorded Future's Insikt Group® identifying 23 vulnerabilities requiring immediate remediation, up from...
Microsoft Copilot Ignored Sensitivity Labels, Processed Confidential Emails
A code bug blew past every security label in the book… and exposed the fatal flaw in how we govern AI.
The post Microsoft Copilot...
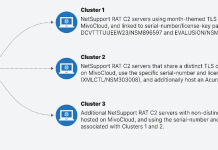
GrayCharlie Injects Malicious JavaScript into WordPress Sites to Deliver NetSupport RAT and Stealc
A threat actor known as GrayCharlie has been compromising WordPress websites since mid-2023, silently embedding malicious JavaScript to push malware onto visiting users. ...
Shai-Hulud-Like Worm Targets Developers via npm and AI Tools
Supply chain worm mimicking Shai-Hulud malware spread via malicious npm packages, targeting AI tools has been identified by security researchers - Read more
2025: The Untold Stories of Check Point Research
Introduction Check Point Research (CPR) continuously tracks threats, following the clues that lead to major players and incidents in the threat landscape. Whether it’s...
Innovate UK cyber startup programme gets £10m funding booster
Graduates of DSIT and Innovate UK's CyberASAP scheme to commercialise cutting-edge cyber research projects have raised nearly £50m in the past decade. -...