Vulnerability monitoring service secures public-sector websites faster
An automated scanning system has cut the time it takes to fix cybersecurity vulnerabilities across public sector IT systems, reducing...
Chrome Gemini Vulnerability Lets Attackers Access Victims’ Camera and Microphone Remotely
A high-severity security vulnerability has been discovered in Google Chrome’s integrated Gemini AI assistant, exposing users to unauthorized camera and microphone access, local file...
2nd March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 2nd March, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
Wynn Resorts, a...
Chrome Unveils Plan For Quantum-Safe HTTPS Certificates
Google Chrome initiates quantum-resistant measures via Merkle Tree Certificates to secure HTTPS - Read more
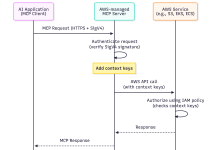
Understanding IAM for Managed AWS MCP Servers
As AI agents become part of your development workflows on Amazon Web Services (AWS), you want them to work with your existing...
NCSC: No increase in cyber threat from Iran, but be prepared
While cyber threat levels remain stable following the outbreak of war in the Middle East at the weekend, at-risk organisations in the UK should...
Sim Studio AI – Unauthenticated OAuth Token Theft
Sim Studio AI - Unauthenticated OAuth Token Theft The `/api/auth/oauth/token` endpoint contains a code path that bypasses all authorization checks when provided with `credentialAccountUserId`...
Sim Studio AI – MongoDB SSRF and Arbitrary Document Deletion
Sim Studio AI - MongoDB SSRF and Arbitrary Document Deletion The MongoDB tool endpoints accept arbitrary connection parameters from the caller without authentication or...
Gradio – Mocked OAuth Login Exposes Server Credentials and Uses Hardcoded Session Secret
Gradio - Mocked OAuth Login Exposes Server Credentials and Uses Hardcoded Session Secret Gradio applications running outside of Hugging Face Spaces automatically enable "mocked"...
Lovora – 495,556 breached accounts
In February 2026, the couples and relationship app Lovora allegedly suffered a data breach that exposed 496k unique email addresses. The data also included...