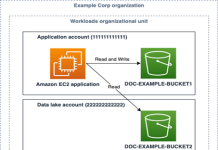
IAM policy types: How and when to use them
June 3, 2022: Original publication date of this post. This post has been updated to add the additional IAM policy types: Resource control...
Navia Data Breach Hits 2.7 Million People, Exposing Sensitive Personal Data
Navia Benefit Solutions says a data breach exposed personal and benefits data tied to 2.7 million people after weeks of unauthorized access.
The post Navia...
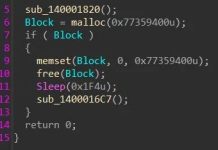
Tax-Themed Google Ads Lead to BYOVD EDR Killer in Huntress-Traced Malvertising Campaign
Every April, millions of Americans rush to file taxes before the deadline — and attackers count on it. A large-scale malvertising campaign, active...
Most Cybersecurity Staff Don’t Know How Fast They Could Stop a Cyber-Attack on AI...
ISACA survey found that confusion over responsibility and lack of understanding around AI cyber-attacks makes containing them difficult - Read more
Faster attacks and ‘recovery denial’ ransomware reshape threat landscape
Mandiant’s M-Trends 2026 report, released today at the RSA Conference, shows that attackers are moving faster, operating more collaboratively, and...
23rd March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 23rd March, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
Navia Benefit Solutions,...
Beers with Talos breaks down the 2025 Talos Year in Review
The Beers with Talos B team (that’s Hazel, Bill, Joe and Dave) break down (sometimes in the literal sense) the 2025 Talos Year in...
2025 Talos Year in Review: Speed, scale, and staying power
The 2025 Talos Year in Review is now available to view online.The pace and scale of adversary activity in 2025 placed sustained pressure on security...
Irish government launches CNI resilience plan
Ireland’s National Strategy on the Resilience of Critical Entities sets out a pathway to improved cyber resilience for the nation’s critical infrastructure, and establishes...
Chromium: CVE-2026-4464 Integer overflow in ANGLE
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2026) for more information. - Read...