ABB EIBPORT
View CSAF
Summary
ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. A firmware update is available that resolves these...
DICOM, Pydicom, GDCM, and Orthanc: A technical tour of what really happens in the...
Over the last decade, DICOM parsing has become an active research topic. The reason is simple: DICOM is both critical and complicated. Hospitals rely...
Citrix NetScaler Memory Overread Vulnerability
Exploitation activity targeting vulnerable Citrix NetScaler ADC and Gateway appliances remains persistent and widespread, with FortiGuard Labs telemetry continuously observing attack attempts from global...
From Exploit Code to Production Detection: Building a CVE-2026-31431 (Copy Fail) detection with Agents
CVE-2026-31431 (Copy Fail) lets any unprivileged user corrupt the Linux page cache via AF_ALG sockets to escalate privileges. This post covers the exploit mechanics...
The Small Model Cliff
CASI Leaderboard, Bias Jailbreak, and Three Coordinated Supply Chain Incidents - Read more
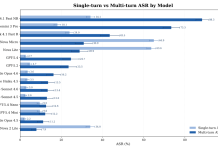
AI models more vulnerable than claimed when faced with iterative attacks
CISOs relying on LLM runtime guardrails and official safety scores when making security decisions about their organizations’ AI usage and...
Report ‘phone hack’ to police or I will do it for you, Labour chair...
Anna Turley gives Reform leader 24 hours to report Russian hacking claim in ‘public and national interest’The Labour chair has given Nigel Farage 24...
GHOST STADIUM Phishing Campaign Targets FIFA World Cup Fans With 300+ Fake Domains
As the 2026 FIFA World Cup draws closer, cybercriminals are moving fast to cash in on the excitement. Researchers have uncovered a massive fraud...
Gladinet Triofox Server Agent Multiple Vulnerabilities
Gladinet Triofox Server Agent Multiple Vulnerabilities Multiple vulnerabilities exist in Gladinet Triofox Server Agent 17.1.10488.57063. CVE-2026-8364 - Missing Authentication for Critical Function (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) Gladinet Triofox Cloud...
The Next AI Security Failure May Start With a Trusted Assistant
AI coding tool flaws highlight the need for data-layer governance, access controls, encryption, and audit logs for AI agents.
The post The Next AI Security...