The State of Cyber Security in Healthcare
The privacy and security concerns associated with digital patient records make the healthcare industry one of the most regulated industries in the United States....
CEO Fraud Continues to Rear Its Ugly Head
As CEO of Centrify, I have been writing about “CEO Fraud” — whereby scammers send emails that impersonate senior executives to obtain money or...
Remotely controlled EV home chargers – the threats and vulnerabilities
We are now seeing signs of a possible shift in the field of personal transport. Recent events such as the ‘dieselgate’ scandal undermine customer...
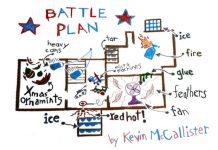
Zero Trust Lessons from a Holiday Classic
Every year when the holidays roll around, I’m amazed at the way shopping deals dominate the headlines. Black Friday and Cyber Monday are annual...
Zero-day in Windows Kernel Transaction Manager (CVE-2018-8611)
Executive summary
In October 2018, our AEP (Automatic Exploit Prevention) systems detected an attempt to exploit a vulnerability in the Microsoft Windows operating system. Further...
Gartner Names Centrify a Leader in Magic Quadrant for Privileged Access Management (PAM)
On December 3, 2018 Gartner released The Magic Quadrant for Privileged Access Management, Q4 2018. Evaluating 14 vendors, Gartner positioned Centrify in the LEADERS...
DarkVishnya: Banks attacked through direct connection to local network
While novice attackers, imitating the protagonists of the U.S. drama Mr. Robot, leave USB flash drives lying around parking lots in the hope that...
APT review of the year
What were the most interesting developments in terms of APT activity throughout the year and what can we learn from them?
Not an easy question...
KoffeyMaker: notebook vs. ATM
Despite CCTV and the risk of being caught by security staff, attacks on ATMs using a direct connection — so-called black box attacks —...