[Video] The TTP Ep 21: When Attackers Become Trusted Users
In this episode of the Talos Threat Perspective, we explore how identity is being used to gain, extend, and maintain access inside environments. Drawing on...
EvilTokens abuses Microsoft device code flow for account takeovers
A new phishing-as-a-service (PhaaS) campaign is abusing Microsoft’s device code authentication flow to gain unauthorized access to user accounts. Sekoia...
Siemens SICAM 8 Products
View CSAF
Summary
Multiple SICAM 8 products are affected by multiple vulnerabilities that could lead to denial of service, namely: - SICAM A8000 Device firmware -...
Yokogawa CENTUM VP
View CSAF
Summary
Successful exploitation of this vulnerability could allow an attacker to login as the PROG user and modify permissions.
The following versions of Yokogawa CENTUM...
Hitachi Energy Ellipse
View CSAF
Summary
Hitachi Energy is aware of a Jasper Report vulnerability that affects the Ellipse product versions mentioned in this document below. This vulnerability can...
How ‘Wikipedia of cyber’ helps SAP make sense of threat data
SAP runs enormous cloud environments for some of the world’s most heavily-regulated organisations, and in the hyperscale era, data security and compliance were becoming...
What’s driving Oracle’s latest job cuts?
Thousands of job losses have been reported, affecting many roles at Oracle Cloud Infrastructure including software engineering and product compliance - Read more
The AI Security Compliance Gap: Fighting Polymorphic Phishing While Staying Regulatory Ready
As cyber threats evolve, organisations face a growing dilemma: how to defend against increasingly sophisticated phishing attacks while staying compliant with expanding data protection...
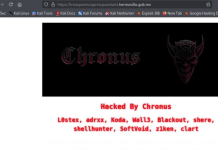
Latin America and the Caribbean Cybercrime Landscape
Executive Summary This report provides an overview of trends and developments in the cybercriminal ecosystem of Latin America and the Caribbean (LAC) in...
Iran Threatens to Attack Apple, Google, and Other US Tech Firms in Middle East
Iran has threatened multiple US tech giants in the Middle East, escalating tensions and raising fears of AI-driven warfare turning physical.
The post Iran Threatens...



![[Video] The TTP Ep 21: When Attackers Become Trusted Users](https://www.dataproof.co.za/wp-content/uploads/2026/04/video-the-ttp-ep-21-when-attackers-become-trusted-users-218x150.jpg)