Stop Breaches with Analytics and Artificial Intelligence
According to Gartner, companies will spend up to $96 billion worldwide on security this year, but research by Centrify and Dow Jones suggests that...
The Global Playing Field is Leveling Out as Europe and Asia Take on More...
The latest DDoS trends include the return of large volumetric DDoS attacks, the rise of application targeted attacks, and businesses in Europe and Asia...
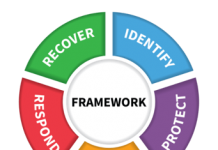
Why the Path Towards Zero Trust Starts with Next-Gen Access
Zero Trust Security has gained a lot of popularity over the last six months. Almost daily you can read articles about this security strategy...
Pocket cryptofarms
In recent months, the topic of cryptocurrency has been a permanent news fixture — the value of digital money has been see-sawing spectacularly. Such...
GDPR and Privacy: How to Earn the Trust of Your Customers and Keep Regulators...
Customer data is the lifeblood of any organisation and the key to unlocking sales and growth. But the data you hold and how you...
Your new friend, KLara
While doing threat research, teams need a lot of tools and systems to aid their hunting efforts – from systems storing Passive DNS data...
Old Dog, New Targets: Switching to Windows to Mine Electroneum
Apache Struts 2 Jakarta Multipart Parser RCE crypto-mining campaign is now targeting Windows, not just Linux systems. - Read more
Real-Life Exposed Privileged Identity Theft
Have you ever had your identity stolen? Credit cards obtained under your name that were not yours?
Most of us have, and what a pain...
Threat Landscape for Industrial Automation Systems in H2 2017
For many years, Kaspersky Lab experts have been uncovering and researching cyberthreats that target a variety of information systems – those of commercial and...