Sodin ransomware exploits Windows vulnerability and processor architecture
When Sodin (also known as Sodinokibi and REvil) appeared in the first half of 2019, it immediately caught our attention for distributing itself through...
How we hacked our colleague’s smart home
In this article, we publish the results of our study of the Fibaro Home Center smart home. We identified vulnerabilities in Fibaro Home Center...
Criminals, ATMs and a cup of coffee
In spring 2019, we discovered a new ATM malware sample written in Java that was uploaded to a multiscanner service from Mexico and later...
ViceLeaker Operation: mobile espionage targeting Middle East
In May 2018, we discovered a campaign targeting dozens of mobile Android devices belonging to Israeli citizens. Kaspersky spyware sensors caught the signal of...
Not-so-dear subscribers
Many people have had a run-in with subscriptions to mobile content providers. They appear out of the blue, and get discovered only when account...
Plurox: Modular backdoor
In February this year, a curious backdoor passed across our virtual desk. The analysis showed the malware to have a few quite unpleasant features....
What kids get up to online
Today’s children navigate the Internet better than adults. They are not afraid to try out new technology, and are quick to grasp new trends...
Platinum is back
In June 2018, we came across an unusual set of samples spreading throughout South and Southeast Asian countries targeting diplomatic, government and military entities....
Zebrocy’s Multilanguage Malware Salad
Zebrocy is Russian speaking APT that presents a strange set of stripes. To keep things simple, there are three things to know about Zebrocy
Zebrocy...
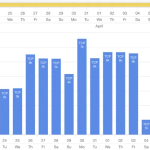
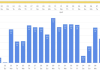
IT threat evolution Q1 2019. Statistics
These statistics are based on detection verdicts of Kaspersky Lab products received from users who consented to provide statistical data.
Quarterly figures
According to Kaspersky Security...