IT threat evolution Q2 2019
Targeted attacks and malware campaigns
More about ShadowHammer
In March, we published the results of our investigation into a sophisticated supply-chain attack involving the ASUS Live...
Recent Cloud Atlas activity
Also known as Inception, Cloud Atlas is an actor that has a long history of cyber-espionage operations targeting industries and governmental entities. We first...
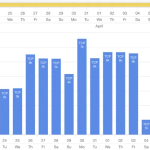
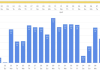
DDoS attacks in Q2 2019
News overview
The second quarter of 2019 turned out to be richer than the first in terms of high-profile DDoS attacks. True, most of the...
APT trends report Q2 2019
For two years, the Global Research and Analysis Team (GReAT) at Kaspersky has been publishing quarterly summaries of advanced persistent threat (APT) activity. The...
Financial threats in H1 2019
Introduction and methodology
Financial cyberthreats are malicious programs that attack users of online banking services, electronic money, cryptocurrency and other similar services, as well as...
How to steal a million (of your data)
Any user data — from passwords for entertainment services to electronic copies of documents — is highly prized by intruders. The reason is simply...
On the IoT road: perks, benefits and security of moving smartly
Kaspersky has repeatedly investigated security issues related to IoT technologies (for instance, here, or here). Earlier this year our experts have even gained foothold...
Turla renews its arsenal with Topinambour
Turla, also known as Venomous Bear, Waterbug, and Uroboros, is a Russian speaking threat actor known since 2014, but with roots that go back...
New FinSpy iOS and Android implants revealed ITW
FinSpy is spyware made by the German company Gamma Group. Through its UK-based subsidiary Gamma International Gamma Group sells FinSpy to government and law...
‘Twas the night before
Recently, the United States Cyber Command (USCYBERCOM Malware Alert @CNMF_VirusAlert) highlighted several VirusTotal uploads of theirs – and the executable objects relating to 2016...