From Code to Runtime: The Critical Role of DAST in Application Security
Regardless of where you’re at in your application security maturity, dynamic application security testing (DAST) is a program staple in a few key ways:It...
Nginx UI – Unauthenticated Backup Download with Encryption Key Disclosure
Nginx UI - Unauthenticated Backup Download with Encryption Key Disclosure The /api/backup endpoint is accessible without authentication and discloses the encryption keys required to...
Delta Electronics CNCSoft-G2
View CSAF
Summary
Successful exploitation of this vulnerability could result in an attacker achieving remote code execution on the device.
The following versions of Delta Electronics CNCSoft-G2...
UAT-9244 targets South American telecommunication providers with three new malware implants
Cisco Talos is disclosing UAT-9244, who we assess with high confidence is a China-nexus advanced persistent threat (APT) actor closely associated with Famous Sparrow.Since...
Spyware suppliers exploit more zero-days than nation states
Exploitation of zero-days by commercial surveillance and spyware developers outpaced exploitation by nation-state actors last year, according to a report - Read more
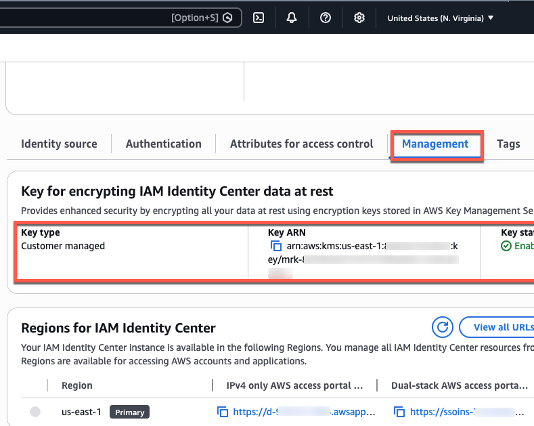
2025 ISO and CSA STAR certificates are now available with one additional service and...
Amazon Web Services (AWS) successfully completed the annual recertification audit with no findings for ISO 9001:2015, 27001:2022, 27017:2015, 27018:2019, 27701:2019, 20000-1:2018, 22301:2019,...
Why AI, Zero Trust, and modern security require deep visibility
AI. Automation. Zero Trust. They dominate every security strategy document. But there’s a truth sitting underneath all three: none of them...
Samsung MagicINFO Server Multiple Vulnerabilities
Samsung MagicINFO Server Multiple Vulnerabilities MagicINFO User Credential Disclosure (CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H)NOTE: Samsung mentioned this item may have been fixed with version 21.1090.1, but we were...
Google Cloud Platform (GCP) Eventarc PE to Service Agent with Pipelines
Google Cloud Platform (GCP) Eventarc PE to Service Agent with Pipelines Tenable Research has identified and responsibly disclosed a critical privilege escalation vulnerability in...
Perplexity AI Browser Flaw Could Let Calendar Invites Access Local Files
Researchers say a vulnerability in Perplexity’s Comet AI browser could expose local files and credentials through malicious calendar invites.
The post Perplexity AI Browser Flaw...