Current password requirement bypass for self password change
CVSSv3 Score: 6.5
An Unverified Password Change vulnerability in FortiSOAR may allow an attacker who gained access to a victim's...
OS command injection in GUI backup options
CVSSv3 Score: 6.9
An improper neutralization of special elements used in an OS command ('OS Command Injection') vulnerability in FortiSandbox...
Capacity to forge authentication cookies
CVSSv3 Score: 7.1
A reliance on cookie without validation or integrity checking vulnerability in FortiWeb may allow an unauthenticated attacker...
Insertion of sensitive information into REST API logs
CVSSv3 Score: 6.3
An insertion of sensitive information into log file vulnerability in FortiOS, FortiProxy, FortiPAM and FortiSRA may allow...
Cofense Delivers Faster, Smarter Phishing Defense with New Capabilities
LEESBURG, Va., December 9, 2025 - Cofense, the leader in intelligence-driven phishing defense, today announced significant advancements across its portfolio, introducing Smart Reinforcement within its...
Phishers Get Creative: The NoteGPT Twist You Didn’t See Coming
By: Hendrix Garcia, Cofense Phishing Defense CenterNoteGPT is an AI-generated tool that converts lengthy lectures, meetings, or videos into concise, easy-to-read notes in just...
GrayBravo’s CastleLoader Activity Clusters Target Multiple Industries
Note: The analysis cut-off date for this report was November 10, 2025 Executive Summary Insikt Group continues to monitor GrayBravo (formerly tracked as...
10 Years of Let’s Encrypt Certificates
On September 14, 2015, our first publicly-trusted certificate went live. We were proud that we had issued a certificate that a significant majority of...
5 Real-Word Third-Party Risk Examples
Key Takeaways Static vendor checks fall short: Traditional, point-in-time third-party risk management practices (e.g. annual questionnaires) leave organizations blind to emerging vendor...
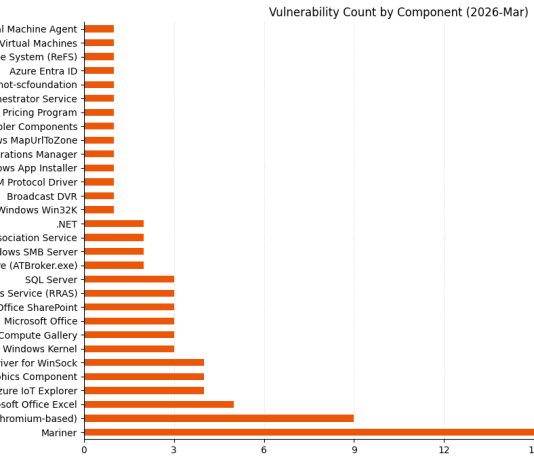
November 2025 CVE Landscape: 10 Critical Vulnerabilities Show 69% Drop from October
November 2025 saw a significant 69% decrease in high-impact vulnerabilities, with Recorded Future's Insikt Group® identifying 10 vulnerabilities requiring immediate attention, down from...