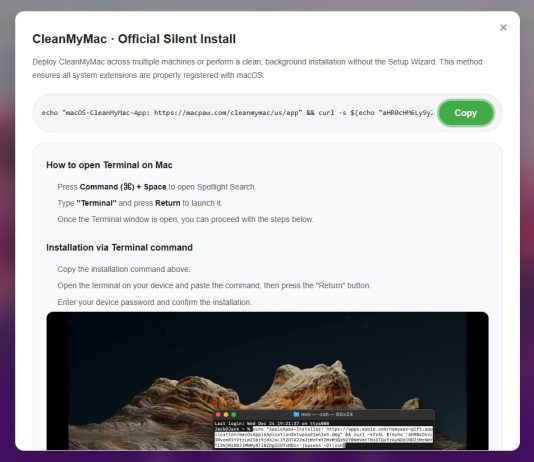
Code Execution in Jupyter Notebook Exports
After our research on Cursor, in the context of developer-ecosystem security, we turn our attention to the Jupyter ecosystem. We expose security risks we...
Imperva Partners with TollBit to Power AI Traffic Monetization for Content Owners
The surge in AI-driven traffic is transforming how websites manage their content. With AI bots and agents visiting sites at unprecedented rates (often scraping...
Inside Ink Dragon: Revealing the Relay Network and Inner Workings of a Stealthy Offensive...
Key Findings
In recent months, Check Point Research has identified a new wave of attacks attributed to the Chinese threat actor Ink Dragon. Ink Dragon overlaps...
Common Holiday Phishing Threats and How to Recognize Them
The holiday season brings a flurry of online shopping, travel plans, and end-of-year workplace activity. With that, it also brings a surge of phishing...
What AWS Security learned from responding to recent npm supply chain threat campaigns
AWS incident response operates around the clock to protect our customers, the AWS Cloud, and the AWS global infrastructure. Through that work,...
Amazon Threat Intelligence identifies Russian cyber threat group targeting Western critical infrastructure
As we conclude 2025, Amazon Threat Intelligence is sharing insights about a years-long Russian state-sponsored campaign that represents a significant evolution in...
2026 Cybersecurity Predictions
Whatever you think will happen… will happen faster and with more acronyms than ever before. - Read more
[R2] Nessus Versions 10.11.1 and 10.9.6 Fix Multiple Vulnerabilities
Nessus Versions 10.11.1 and 10.9.6 Fix Multiple Vulnerabilities Arnie Cabral Mon, 12/15/2025 - 09:48
Nessus leverages third-party software to help provide underlying functionality....
15th December – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 15th December, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
The Indian government...
What’s Next for Enterprise Threat Intelligence in 2026
Introduction The cybersecurity landscape is rapidly growing in scale and complexity. Enterprises face a rising tide of sophisticated threats that cannot be contained...