Raaga – 10,225,145 breached accounts
In December 2025, data allegedly breached from the Indian streaming music service "Raaga" was posted for sale to a popular hacking forum. The data...
19th January – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 19th January, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
Spanish energy company...
Pass’Sport – 6,366,133 breached accounts
In December 2025, data from France's Pass'Sport program was posted to a popular hacking forum. Initially misattributed to CAF (the French family allowance fund),...
Microsoft January 2026 Security Update Causes Credential Prompt Failures in Remote Desktop Connections
Microsoft has released an out-of-band emergency update to resolve a critical issue affecting Remote Desktop connections on Windows client devices. The problem emerged immediately...
Let’s Encrypt has made 6-day IP-based TLS certificates Generally Available
Let’s Encrypt, a key provider of free TLS certificates, has rolled out short-lived and IP address-based certificates for general use. These new options became...
UAT-8837 Critical Infrastructure Attack
What is the Attack? An active campaign has been linked, with...
AppGuard Critiques AI Hyped Defenses; Expands its Insider Release for its Next-Generation Platform
A new Top 10 Cybersecurity Innovators profile by AppGuard has been released, spotlighting growing concerns over AI-enhanced malware. AI makes...
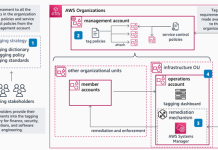
Implementing data governance on AWS: Automation, tagging, and lifecycle strategy – Part 2
In Part 1, we explored the foundational strategy, including data classification frameworks and tagging approaches. In this post, we examine the technical...
Implementing data governance on AWS: Automation, tagging, and lifecycle strategy – Part 1
Generative AI and machine learning workloads create massive amounts of data. Organizations need data governance to manage this growth and stay compliant....
Chromium: CVE-2026-0907 Incorrect security UI in Split View
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2024 ) for more information. -...