Denis and Co.
In April 2017, we published a detailed review of a malicious program that used DNS tunneling to communicate to its C&C. That study prompted...
Centrify to Discuss Zero Trust Security at the ICIT 2018 Winter Summit
Following the high-profile breach of the US Office of Personnel Management (OPM), which exposed the personal data of millions of Americans, the House of Representatives’...
4 Months to Go: A New Year GDPR Checklist
As we enter the New Year, IT and security leaders have most likely been glued to revelations of major new CPU-level vulnerabilities Meltdown and...
Data Breaches Plague Organizations for Years
Once an organization’s network is breached, extinguishing the flames is just the first step in a long, painful and costly journey to recovery. There’s...
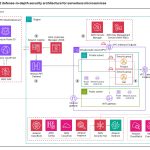
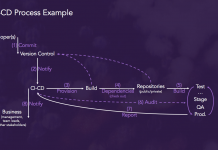
Security Strategies for DevOps, APIs, Containers and Microservices
More and more IT professionals see DevSecOps, a practice which integrates security measures earlier in the development process to improve production code quality, as...
The Emerging Importance of Securing Access to AWS
With 50,000 attendees, over 1,000 breakout sessions and countless sponsors and exhibitors, the 2017 AWS re:Invent conference in Las Vegas was one of the...
Skygofree: Following in the footsteps of HackingTeam
At the beginning of October 2017, we discovered new Android spyware with several features previously unseen in the wild. In the course of further...
Data Privacy Day
- Read more
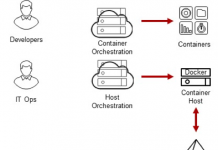
Centrify Identity Services: Securing Docker and Containers
Introduction
We are excited to announce that Centrify now supports CoreOS Container Optimized Linux which several of our customers are using as part of their...
Cloud Database Migration Peer Insights [Report]
Not long ago, for security, compliance or other reasons, it was unthinkable for many regulated organizations to move sensitive data into the cloud. It’s...









![Cloud Database Migration Peer Insights [Report]](https://www.dataproof.co.za/wp-content/uploads/2018/01/cloud-database-migration-peer-insights-report-218x150.png)