Centrify Named a March 2019 Gartner Peer Insights Customers’ Choice for Privileged Access Management
At Centrify we are proud of our customers and the success they experience with our solutions. Today we are proud that our customers are...
Time to Retire “The Year Of…” at RSA 2019
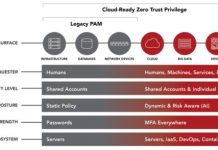
Today at the RSA Security Conference, we announced Centrify’s Cloud-Ready Zero Trust Privilege Services architecture, including a wide range of enhancements that redefine legacy...
Centrify RSA Booth 6445: Where Zero Trust Privilege Partners Take the Stage
If there was one clear takeaway from the 2018 RSA Conference, it was that Zero Trust was ready to take off.
It seemed like everywhere...
Start Your Engines! It’s Zero Trust Privilege Test Drive Season!
As organizations struggle to protect the ever-expanding attack surface, they not only have to secure access to infrastructure, databases, and network devices, but also...
NEW CENTRIFY SURVEY: Too Much Privilege, Not Enough PAM Powered by Zero Trust
I’m both a technology guy, and a numbers guy.
I have Bachelor of Science degrees in both Accounting and Computer Science. I’ve held the CFO...
Gartner Names PAM a Top Security Project (AGAIN!) in 2019
Last June at the 2018 Gartner Security & Risk Management Summit, the analyst firm issued a “Smarter with Gartner” paper outlining the Top 10...
Five Reasons to Visit Centrify Booth #N6445 at RSA 2019
The 2019 RSA Conference is just around the corner, coming up March 4-8 at the Moscone Center in San Francisco!
If you’ve never attended an...
Putting the Reins in Good Hands
After over 300 blog posts as CEO of Centrify, this will be my last Centrify blog post.
The reason is because after having co-founded Centrify...
The State of Cyber Security in Healthcare
The privacy and security concerns associated with digital patient records make the healthcare industry one of the most regulated industries in the United States....
CEO Fraud Continues to Rear Its Ugly Head
As CEO of Centrify, I have been writing about “CEO Fraud” — whereby scammers send emails that impersonate senior executives to obtain money or...