As of April 15, 2026, NIST enriches only CVEs that appear in the CISA Known Exploited Vulnerabilities catalog, federal government software, or software designated critical under Executive Order 14028. Everything else carries a “Lowest Priority” status: no CVSS score, no affected product mappings, no weakness classification. NIST enriched roughly 42,000 CVEs in 2025, and submissions in early 2026 are running about a third higher year-over-year. Industry estimates suggest the prioritized categories will cover only 15–20% of anticipated CVE volume going forward.
For teams whose vulnerability management workflows depend on CVSS scores from NVD, this could create an operational gap. The CVEs in the unenriched backlog can signify real vulnerabilities affecting real software. They don’t necessarily stop mattering because NIST didn’t get to them.
Recorded Future does not believe that the solution is to source CVSS scores faster. Instead, Recorded Future endeavors to provide the signals that actually reflect attacker behavior. CVSS was designed to characterize the technical properties of a vulnerability — attack vector, complexity, required privileges, potential impact. CVSS was not designed with patch prioritization as a prime concern. This distinction has always existed; the growing gap in NVD enrichment increases the importance of the right intelligence and insights that can capture attacker behavior in real time.
Where vulnerability risk actually originates
Exploit code surfaces on GitHub. Proof-of-concept development gets discussed in offensive security forums and underground communities. Ransomware operators evaluate which vulnerabilities fit their deployment pipelines. Threat actors incorporate specific CVEs into their toolkits and begin scanning in search of exploitable targets.
At some point during or after that sequence, a CVE gets assigned and, under the previous policy, would eventually be enriched by NVD. By the time a practitioner sees a CVSS score in their scanner, the risk may already have materialized.
The delay between attacker use and the assignment of a CVE and CVSS score is not a new dynamic. For this reason, Recorded Future’s vulnerability Risk Scores were never built to depend on NVD enrichment.
The intelligence that determines whether a vulnerability is dangerous originates in the technical communities, underground markets, exploit repositories, and malware ecosystems where attackers work. It does not come from institutional databases processing CVEs up to weeks or months post-assignment. NVD’s policy change doesn’t create a gap in Recorded Future’s coverage because NVD is not the primary signal behind Recorded Future Vulnerability Intelligence.
What the model actually weighs
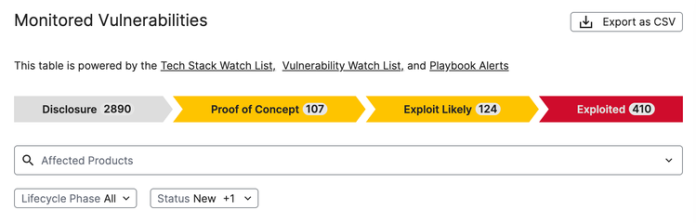
Recorded Future’s risk scoring maps directly to the vulnerability weaponization lifecycle. Many of the signals fire based on where a CVE sits on that path, not on what NIST has or hasn’t scored.

The signals that carry the most weight are those tied to active exploitation in the wild — malware samples observed by Recorded Future’s collection infrastructure, ransomware operations validated by Insikt Group® analysts, and other direct evidence of attacker use. Confirmed exploitation activity carries the most weight in the model, regardless of a CVE’s CVSS score. These are the signals that answer the question practitioners actually need answered: is someone using this right now?
Below active exploitation, the model tracks proof-of-concept availability, including the distinction between a verified and unverified PoC. Verified exploit code that demonstrates remote execution is a materially different signal from an unverified proof of concept of unknown reliability. As an example, exploit code on GitHub is not theoretical risk; it usually compresses the time between disclosure and weaponization. Recorded Future Risk Scores treat it accordingly.
In addition to these collection and analytic capabilities, Recorded Future tracks web reporting about a CVE before NVD has published enrichment data. For the majority of new CVEs going forward, this pre-NVD signal may be the earliest structured intelligence available anywhere. A CVE that NIST has marked Lowest Priority can still accumulate signals across many dimensions. As a result, the absence of a CVSS score in NVD doesn’t create a blind spot in Recorded Future’s assessment.
CVSS still matters. It just isn’t the foundation.
CVSS scores flow into the model from multiple sources. Many CVE numbering authorities (CNAs) supply CVSS scores at the point of submission, and CVSS coverage across published CVEs remained above 90% in 2025 even as NVD’s independent enrichment narrowed. That doesn’t mean CNA-supplied scores are interchangeable with NVD’s. Academic analyses of dual-scored CVEs have documented divergence rates above 50% throughout the past decade, reaching 70% in 2023, with disagreements sometimes large enough to move a vulnerability across severity tiers. For CVEs where neither NVD nor a CNA has provided scoring, Recorded Future independently assigns scores through its own analysis. CVSS occupies one position in the model, alongside signals grounded in observable attacker behavior, and those signals operate independently of whether a CVSS score exists at all.
What to do with this
Audit where your prioritization signals come from. If your program is relying entirely or primarily on CVSS scores pulled from NVD, you may have exposure, not just from the existing backlog, but from every new CVE entering the ecosystem under the new policy.
Recorded Future Vulnerability Intelligence, as a part of the Cyber Operations solution, scores every CVE against the full signal set — exploitation activity, malware and ransomware associations, proof-of-concept availability, threat actor targeting, and analyst-validated intelligence. All independent of NVD’s enrichment pipeline. See this prioritization and automation in action with this click-through tour.
See how Vulnerability Intelligence integrates with your existing vulnerability management workflow — request a demo.