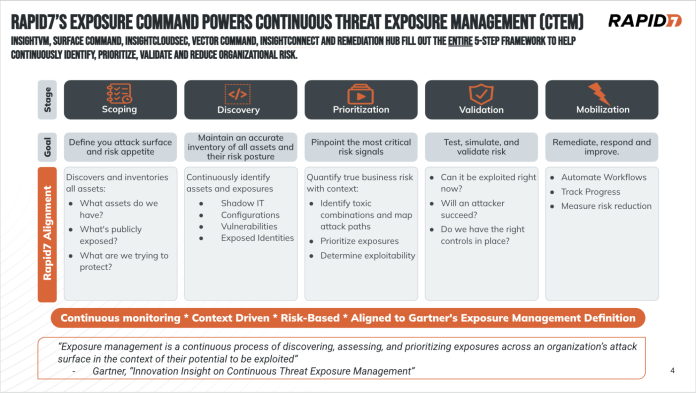
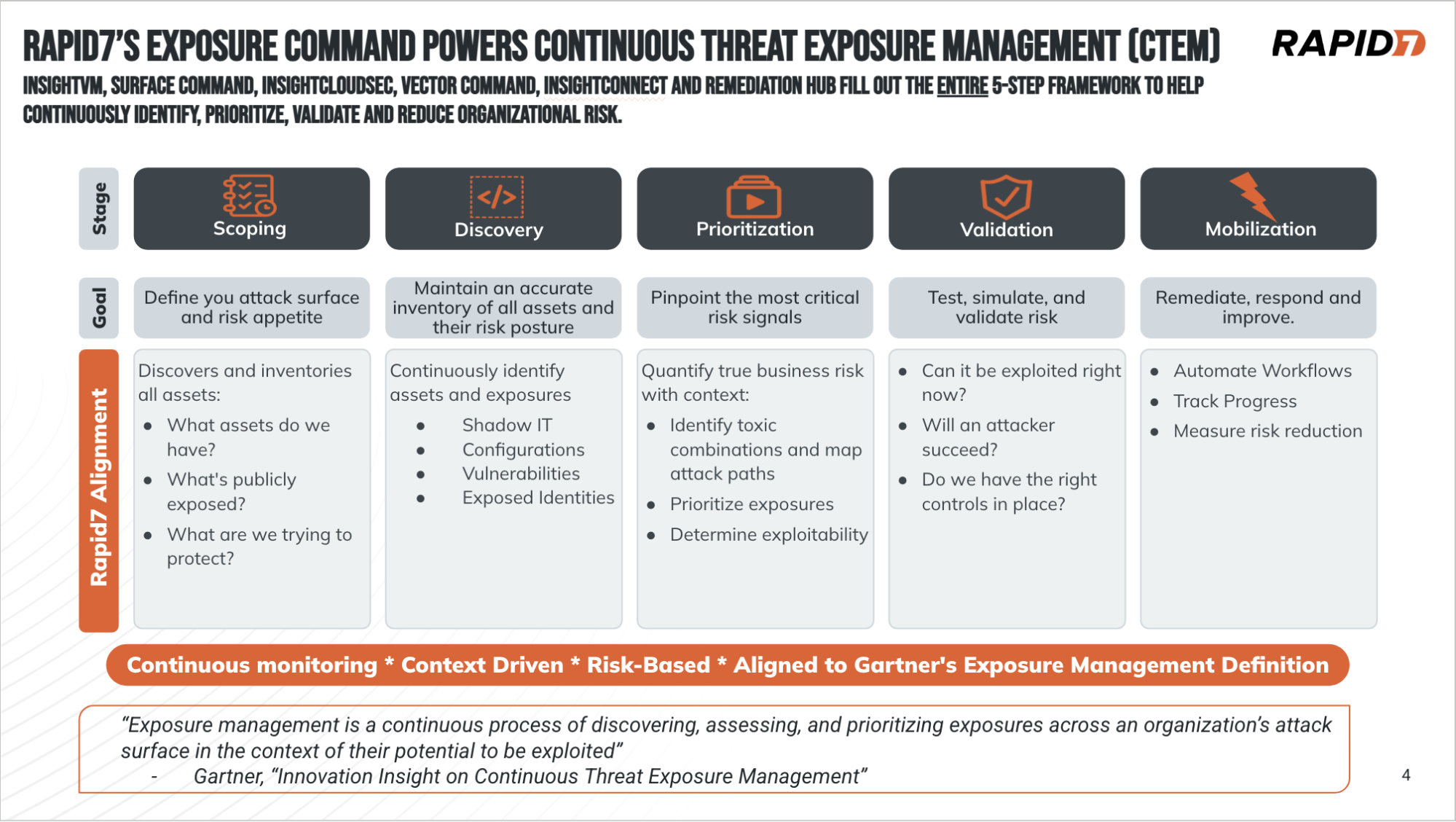
Let’s be honest, the patching window just shrank to something no practitioner or organization can keep up with. Organizations now need to operate in an environment that must assume breach, which means fundamentals like attack surface management, micro-segmentation, identity management, and attack path validation – aka a few core pillars of CTEM – just became the most important initiatives within the cybersecurity department. Rapid7 is the only vendor that provides a truly unified platform to master Continuous Threat Exposure Management (CTEM).
How Rapid7 satisfies all 5 steps of the CTEM Framework
Steps 1 and 2: Scoping and Discovery
Achieving full visibility
Rapid7 eliminates “unknown unknowns” by providing line-of-sight into 100% of your hybrid attack surface.
-
Surface Command (CAASM): We establish a single source of truth by unifying asset and identity inventory from over 200 third-party vendors and native sources.
-
Vulnerability Management: Our full-stack active scanning discovers shadow IT hidden within your enterprise network.
-
External Attack Surface Management (EASM): We scan the entire IPv4 space of the internet to automatically track changes to registered domains and public networks so you can map your external kingdom.
-
Unified CNAPP (Cloud Security): Our platform provides real-time, agentless visibility into every resource running across your multi-cloud environment (AWS, Azure, GCP, and Kubernetes). Through Event-Driven Harvesting (EDH), we identify infrastructure changes in under 60 seconds. This allows us to map not just the assets, but the complex identities and permissions that define your cloud risk.
Step 3: Prioritization
Moving beyond static scores
We replace generic risk scores with Active Risk and Threat-Aware Context. Our platform automatically prioritizes vulnerabilities based on real-world exploitability data from Rapid7 Labs and the Exploit Prediction Scoring System (EPSS). We are also able to incorporate your own organization’s tagging infrastructure to properly contextualize your enterprise so you focus on what matters most.
Step 4: Validation
Continuous human-led red teaming
This is where Rapid7 truly stands apart from automated-only vendors or point-in-time pen tests. Vector Command provides the expert human logic needed to bypass compensating controls like WAFs that stop automated tools cold. This gives Rapid7 the ability to answer the question: “How would an attacker get in?” We fully map the attack chain from the external to the internal so you have insight into where your controls are weakest.
Ed Montgomery at Rapid7 has written extensively about the power of Vector Command – you can find his blogs here.
Here’s a sampling of a couple of those stories:
-
The Telerik UI Example: While a scanner flags an old version of Telerik, our operators discovered they could bypass a WAF by splitting a malicious payload into 118 individual, “harmless” fragments. We bypassed the WAF and this achieved full remote code execution that a time-boxed, two-week pentest would never have uncovered. An automated scan might have flagged the outdated telerik as something notable but it was really the configuration of the WAF that allowed us to bypass. Something an automated scan would never have found.
-
SaaS Phishing: Our team used a misconfigured public Jira instance that allowed self-registration to hijack an Office 365 session and move laterally through internal trust. This validated that the true risk was a SaaS misconfiguration, not a patchable CVE.
Step 5: Mobilization
Instant response and remediation
We don’t just find problems; we close the loop with integrated action.
-
Cloud Runtime Security (CADR): Powered by our partnership with ARMO, our eBPF-based sensor can shut down an attack in seconds by killing malicious processes or pausing containers at the moment of detection.
-
Automation (SOAR): InsightConnect and our “Bot Factory” in CNAPP trigger automated remediation workflows to lock down S3 buckets or disable compromised users instantly.
-
Remediation Hub: We provide a centralized, vendor agnostic action-driven list of prioritized fixes to coordinate seamlessly with IT teams.
The new standard: From weeks to minutes
If your CTEM strategy relies on static tools and annual checkboxes, you are not just behind the curve. You are operating in a completely different era. By unifying the full visibility of Surface Command with the critical thinking of Vector Command and the instant response of our Cloud Runtime capabilities, Rapid7 empowers you to take command of your attack surface.
Do not wait for a 118 single bit request bypass to prove your defenses are porous. Move from a posture of passive observation to one of preemptive security.