Security researchers from Georgia Tech have observed a surge in reported CVEs for which the flaw was introduced by AI-generated code – Read more
Latest article
Regional routing for AWS access portals: Implementing custom vanity domains for IAM Identity Center
AWS IAM Identity Center provides a web-based access portal that gives your workforce a single place to view their AWS accounts and...
Meet Fragnesia, the third Linux kernel vulnerability in a month
Linux admins reeling from handling last month’s CopyFail and last week’s Dirty Frag kernel vulnerabilities have a new headache to...
Microsoft Foundry Toolkit for VS Code: Command Injection via Python Interpreter Path Leading to...
Microsoft Foundry Toolkit for VS Code: Command Injection via Python Interpreter Path Leading to Arbitrary Code Execution Microsoft Foundry Toolkit for VS Code (formerly...
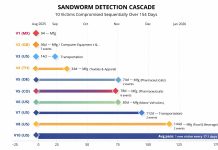
Sandworm Hackers Pivot From Compromised IT Systems Toward Critical OT Assets
A Russian state-sponsored hacking group known as Sandworm has been caught making a calculated pivot from compromised IT networks into operational technology systems that...